Vercel Flags and Sandbox Egress: Ship Safer Now
Two decisions dominate every release: how safely you can roll out, and how tightly you can lock down. With Vercel Flags entering public beta on February 11, 2026, advanced egress controls for Sandbox, and automatic revocation of leaked Vercel API credentials announced February 9, 2026, Vercel just made both moves easier to execute without bolting on more vendors. If you deploy on Vercel—or run Next.js—these are worth adopting this month. (vercel.com)
What actually shipped—and why it matters
Three concrete changes landed in the past two weeks:
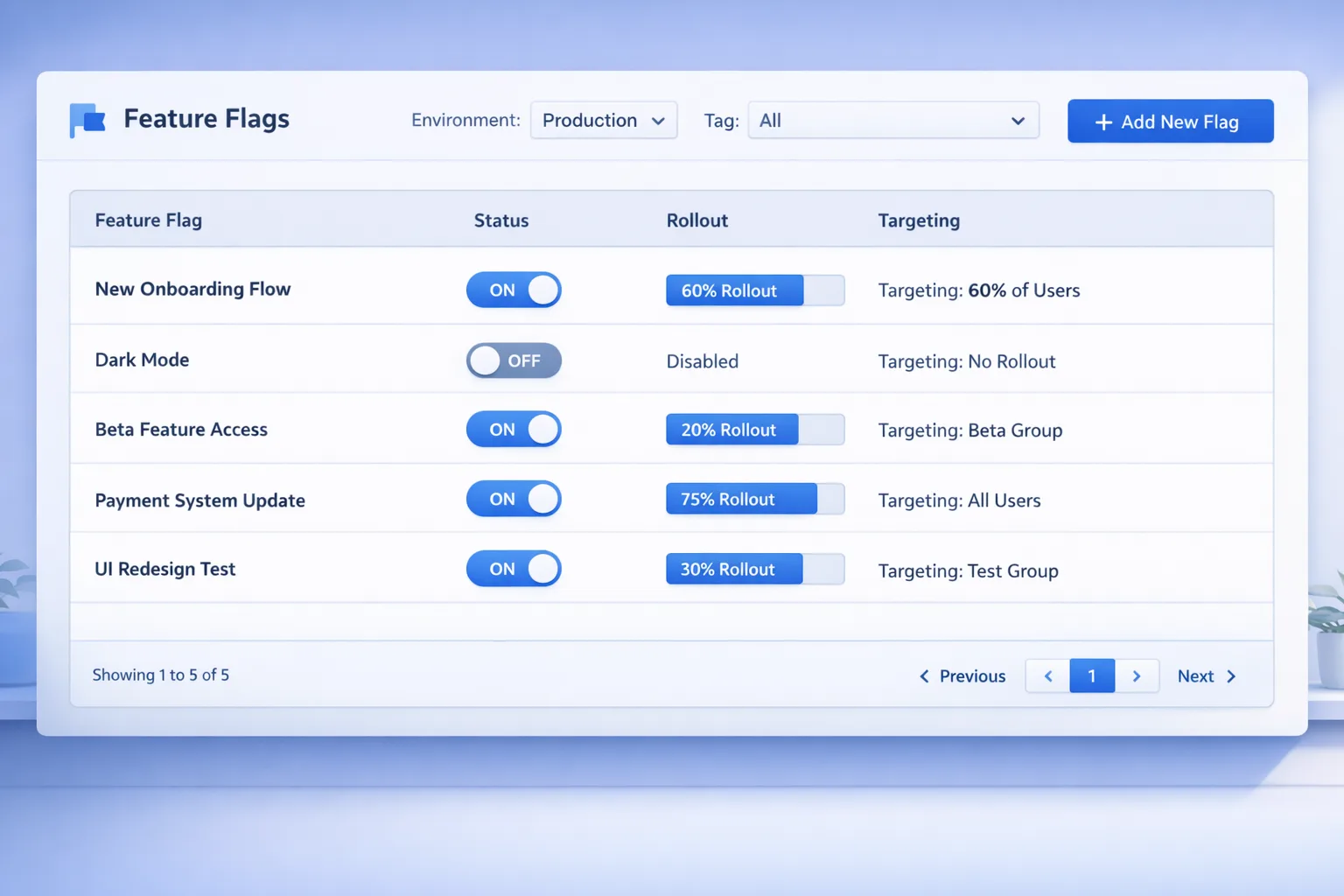
1) Vercel Flags (public beta) puts a first‑party feature flag provider in your dashboard with SDK support, targeting/segments, and a clean price: $30 per 1M flag requests ($0.00003 per event). Flags evaluate close to users with globally replicated configs, so you can test in production and roll back instantly—without wiring yet another service. (vercel.com)
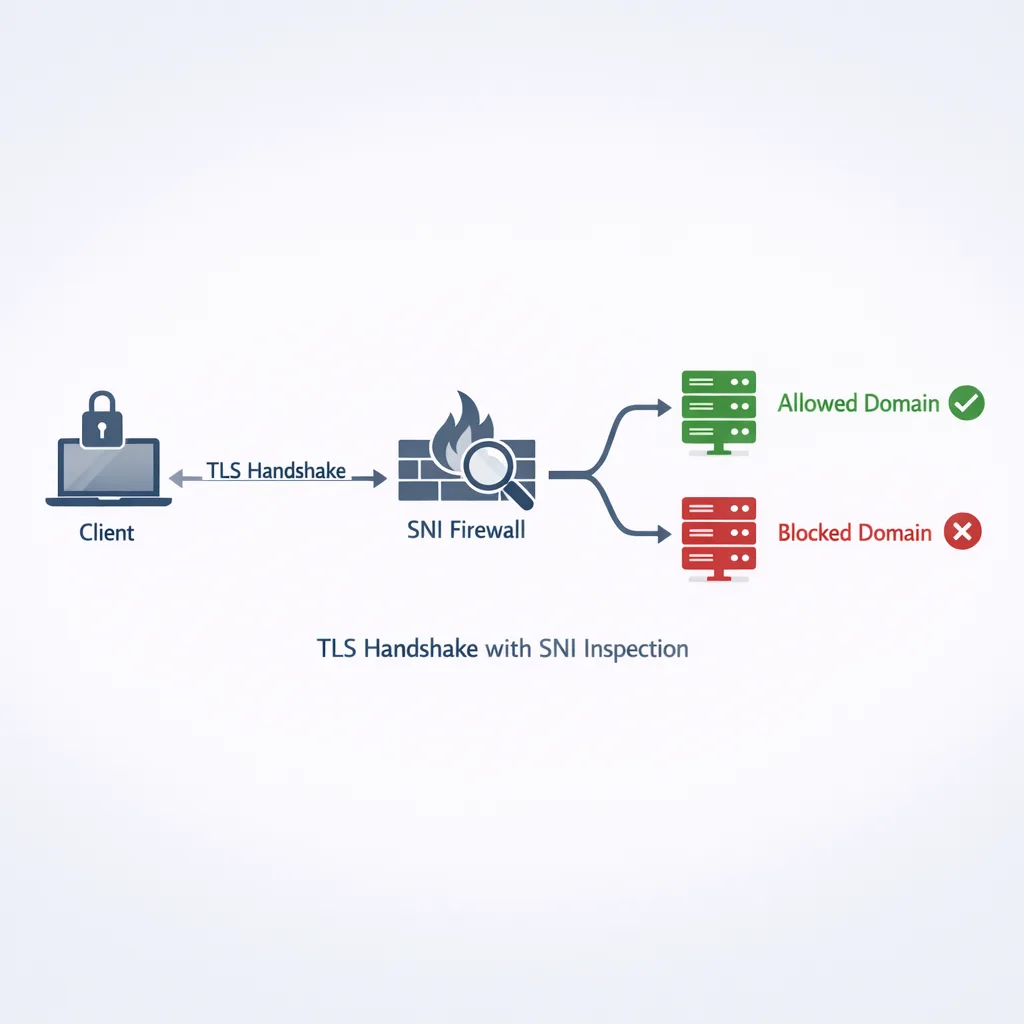
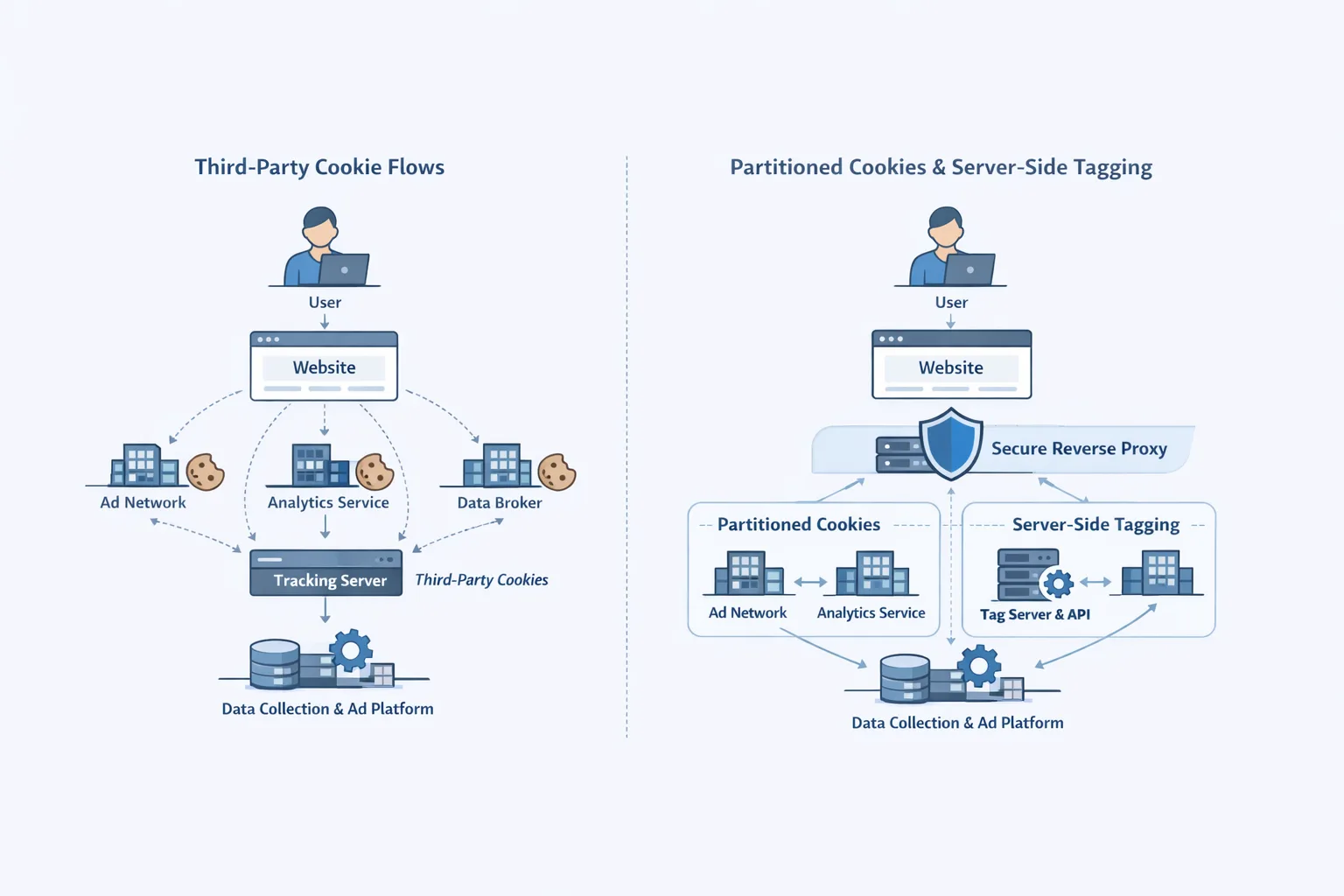
2) Sandbox egress firewall (SNI + CIDR) lets you enforce outbound network allowlists on untrusted or AI‑generated code. Because it peeks SNI during the TLS handshake, it can block calls by hostname without breaking non‑HTTP protocols; non‑TLS fallbacks use CIDR. That’s the right level of granularity for today’s CDN‑heavy internet. (vercel.com)
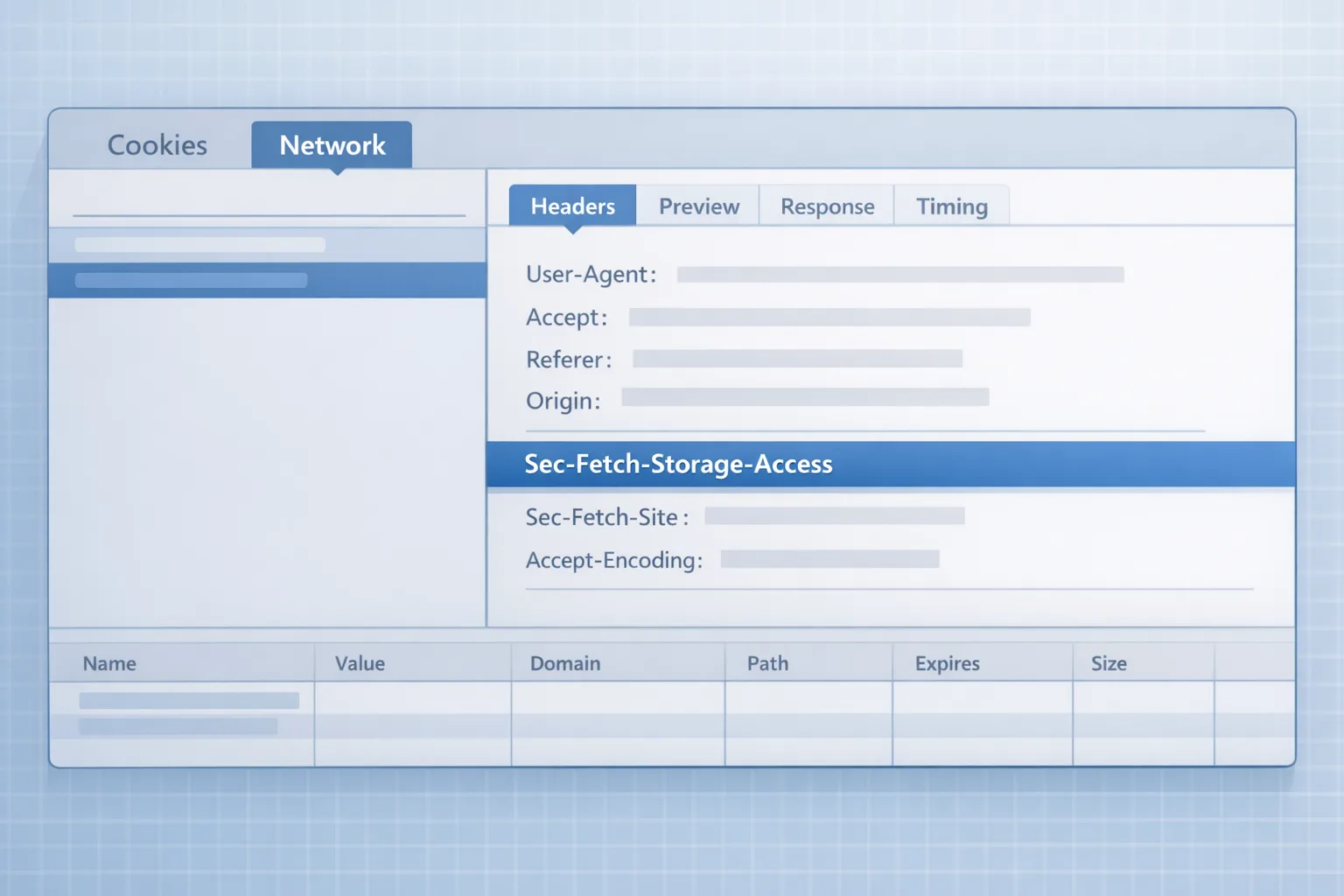
3) Token auto‑revocation means any Vercel token or API key that hits public GitHub, gists, or npm gets revoked automatically, and you get notified. New token prefixes (like vcp for personal tokens) make dangerous strings easier to spot during reviews. Combined with GitHub secret scanning, this cuts time‑to‑contain dramatically when a developer accidentally pushes creds. (vercel.com)
How to use Vercel Flags in production (without breaking flow)
Here’s the thing: flags only help if your team actually uses them on the path to prod. Start with the smallest loop that proves value in a week.
1) Define one product bet and guard it with a flag
Pick a visible but non‑critical change—the redesigned dashboard header, a new pricing card, or an auth hint. Create a boolean flag for showNewHeader with a default of false. Add a percentage rollout to 5% of users plus a “Team” segment for internal accounts. Use the framework adapter so the check is cheap and consistent across SSR/edge. (vercel.com)
2) Wire it to the app using the SDK (and keep usage readable)
Within Next.js or SvelteKit, read the flag once per request and branch to the new component. When you’re tempted to nest flags, step back: long if‑trees are change debt. Model “experiment variants” as a single enum flag instead of three booleans if you’re A/B/n testing.
3) Connect to the analytics you already use
Flag‑aware analytics close the loop. If you’re on Vercel Web Analytics, you can annotate events with evaluated flags to compare conversion/error deltas by variant without custom plumbing. That enables “turn up to 20% if error rate delta < 0.1% and conversion delta ≥ 1%.” (vercel.com)
4) Ship a reversible change every day for two weeks
Trunk‑based development shines when you can merge incomplete work behind flags daily. Treat “flag off but merged” as the happy path; feature branches older than a week should be a smell. (vercel.com)
Pricing and counting gotchas
Flags are billed per flag request, defined as any request to your app that reads a flags config—one request can evaluate multiple flags and still count once. Watch server‑side rendering loops and cron tasks; memoize within a request. At $30 per million, most SaaS teams will spend tens of dollars per month for meaningful coverage. (vercel.com)
People also ask: Can Vercel Flags replace my existing provider?
Maybe. If you want native integration, OpenFeature compatibility, and straightforward pricing inside the same platform that hosts your app, Vercel Flags will feel compelling. If you rely on deep experimentation tooling across mobile, web, and back‑end microservices—or advanced governance/approvals—keep your incumbent for now and pilot Flags on a single surface. Migration is a series of dual‑writes and read‑shadows, not a big‑bang cutover. (vercel.com)
Lock down AI and untrusted code with Sandbox egress rules
Running generated code safely is about more than CPU/memory limits. The new SNI‑aware egress controls let you dial the blast radius down to the hostnames your workload must reach—blocking everything else at the TLS handshake. That prevents data exfiltration to random pastebins, ad‑hoc LLM APIs, or a typo‑squatted domain that happens to share an IP block with something you trust. (vercel.com)
Practical setup that takes under an hour
Start by listing the minimum outbound hosts your sandboxed tasks truly need: your LLM gateway (ai-gateway.vercel.sh), object storage, and your primary API. Add wildcards for CDN fronted domains you control. Block everything else. The allowlist lives with the Sandbox creation code, so changes get code‑reviewed like everything else. (vercel.com)
Edge cases to expect:
- Some third‑party SDKs resolve to rotating hostnames. Use precise wildcards scoped to the vendor’s documented domains, not
*.*. - For legacy non‑TLS protocols, fall back to CIDR—but document why and set a review reminder.
- Watch for DNS‑overrides inside VPC/VNet setups; confirm that what your sandbox resolves is what you intended to allow.
Pair this with Vercel’s platform WAF and DDoS protections for the inbound path and you’re stacking defense‑in‑depth on both sides of your app boundary. (vercel.com)
Tokens will leak—now they’re auto‑revoked. Harden your CI anyway.
Automatic revocation is a lifesaver when (not if) a token slips into a public repo, gist, or npm package. GitHub’s secret scanning picks up the hit, and Vercel revokes the exposed credential immediately, notifying your account. That shortens the window for abuse from “hours or days” to “minutes.” The new token prefixes—like vcp_, vci_, and vck_—also make code reviews and log scrubs more obvious. (vercel.com)
But there’s a catch: revocation is reactive. You still need to prevent long‑lived tokens from becoming your default integration strategy. Prefer short‑lived credentials, narrow scopes, and provider‑issued tokens inside your CI/CD. GitHub already revokes leaked PATs automatically, and secret‑scanning partners can yank other providers’ creds as well—assume your security story will be judged on how quickly you rotate. (docs.github.com)
What I tell teams: if your build system still holds a user’s personal Vercel token, you’re one offboarding away from a production freeze. Move to team‑owned tokens, rotate quarterly, and inventory who can mint them.
CI patterns that hold up under pressure
• Secrets in one place. Keep deployment hooks and API keys in your CI’s secrets store, not sprinkled across multiple repos. Enforce branch protection so only reviewed workflows can reach deploy rights.
• Short‑lived or just‑in‑time access. When possible, prefer ephemeral credentials exchanged at job start over long‑lived static tokens stored in Git. The fewer hours a token is valid, the less attractive it is to an attacker skimming public forks.
• Prefix audits. Teach reviewers to scan for vcp_, vci_, vck_ strings. Humans still catch what scanners miss, especially in screenshots, terminal recordings, and pasted logs. (vercel.com)
The Ship‑Fast, Lock‑Down Framework
Use this lightweight framework to adopt all three updates over two sprints. Treat it like an operational play, not a side quest.
Sprint 1: Control blast radius
Day 1–2: Pick one feature and gate it with Vercel Flags. Add an internal segment and 5% external rollout. Wire evaluation at the request boundary so SSR and edge functions get the same state. (vercel.com)
Day 3–4: Turn on Sandbox egress rules for any job that executes user‑generated or AI‑generated code (formatters, data transforms, preview builders). Allowlist only your LLM gateway, storage, and first‑party APIs. Verify with an intentional “blocked” call. (vercel.com)
Day 5: Rotate tokens. Replace any user‑owned Vercel tokens in CI with team‑owned ones. Document where they live, who created them, and the rotation date. Confirm auto‑revocation alerts are reaching the right Slack/Email group. (vercel.com)
Sprint 2: Close the feedback loop
Day 6–7: Annotate analytics with flag variants. Define the decision rule that moves a feature from 5% to 25% (e.g., no regression in p95 latency and error rate; +1% conversion). (vercel.com)
Day 8–9: Codify egress policy. Represent allowlists as code, add tests for disallowed destinations, and make “egress review” part of the PR template for Sandbox jobs. (vercel.com)
Day 10: Secret hygiene. Audit repos for historical leaks, delete stale tokens, and enforce repo‑level and org‑level secret scanning. Make the new prefixes part of your grep list. (docs.github.com)
Data points to baseline your rollout
• Release dates: Flags public beta and Sandbox egress blog/changelog posts landed Feb 11, 2026; token auto‑revocation published Feb 9, 2026. That’s fresh—and safe to act on now. (vercel.com)
• Price: Flags at $30 per 1M flag requests; a single request can evaluate multiple flags and still count once. Translate that to “pennies per experiment per thousand visits.” (vercel.com)
• Egress coverage: SNI‑based filtering covers nearly all TLS traffic; non‑TLS fallbacks to CIDR exist for the rest. That’s the practical sweet spot for today’s services. (vercel.com)
Common questions from teams
Will Sandbox egress rules slow my jobs down?
The decision happens at the TLS handshake, not deep packet inspection mid‑stream, so the latency impact is negligible compared to remote network hops. You’ll notice it only when something is blocked—which is the point. (vercel.com)
What happens if a valid token is leaked in a private repo?
GitHub auto‑revokes tokens leaked in public repos and gists; in private repos, you still need to act on secret‑scanning alerts. With Vercel’s new integration, leaked Vercel tokens in public spaces are revoked automatically; keep rotation muscle memory for everything else. (docs.github.com)
Can I bring another flag provider?
Yes—Flags supports OpenFeature, so you can standardize evaluation across stacks even if you keep a third‑party provider for parts of the estate. That’s helpful during migrations and hybrid setups. (vercel.com)
Let’s get practical: a minimal implementation checklist
- Create two flags: one boolean (enableNewNav), one enum (cartExperiment: control|variantA|variantB). Evaluate at SSR boundary.
- Add a “5% public + 100% internal” targeting rule on day one.
- Enable client‑side event annotations for flags, and define success thresholds.
- Stand up a Sandbox egress policy with three allowlisted hosts; add a failing test for
example.comto confirm enforcement. - Rotate all user‑owned Vercel tokens used in CI to team‑owned; document owners and expiry.
- Subscribe your on‑call channel to revocation alerts; dry‑run by intentionally scanning a fake token format.
What to do next (this week)
• Book a 60‑minute working session with your lead and a product owner. Pick the first flag, define the rollout rule, and merge by end‑of‑day.
• Harden your untrusted code path. Map every workflow that runs code you didn’t write (AI transforms, user scripts, importers) and enable Sandbox egress allowlists for those first.
• Make creds boring again. Inventory Vercel tokens, delete stale ones, and move to team‑owned creds with a rotation date. Confirm the new prefixes are part of your code‑review checklist. (vercel.com)
Where Bybowu can help
If you want a fast, low‑risk path to production flags, egress controls, and CI hardening, our team does this every week. Start with a short discovery call and we’ll map a two‑sprint plan around your stack. See what we ship on our project portfolio, how we scope engagements on what we do, and the accelerators in our services catalog. Or dig into adjacent playbooks on our blog.
Zooming out: feature flags, outbound allowlists, and automatic secret revocation aren’t luxuries anymore—they’re the guardrails that let small teams move like big ones, and big teams ship like startups. Adopt them once and you’ll wonder how you shipped without them.



Comments
Be the first to comment.