Node.js EOL 2026: Your 45‑Day Upgrade Playbook
Two dates define the immediate future of your backend: April 1, 2026 (when Node 25 enters maintenance ahead of a June 1 end of life), and April 30, 2026 (when Node.js 20 stops receiving security updates). Treat this as a product deadline, not an IT chore. The fastest, lowest‑risk move is upgrading to Node 24 LTS. This guide distills what actually changes, where teams stumble, and a practical 45‑day plan to land the upgrade without firefighting.

What exactly changes between April 1 and June 1?
Here’s the thing: after April 1, 2026, the Node 25 line moves into maintenance. That means fewer updates and only critical fixes. One month later—on April 30—Node 20 LTS exits security support, which removes your safety net for new vulnerabilities. And on June 1, 2026, Node 25 reaches end of life entirely. If your production relies on 20 or 25, you’re on borrowed time for security, compliance, and partner integrations.
Zooming out, Node 24 LTS remains supported with security updates through April 30, 2028. That’s runway your roadmap can actually use—enough for platform rewrites, database migrations, and performance work without juggling emergency patches.
Why this matters to product teams (not just platform ops)
Audit findings and vendor checks are already keyed to supported runtimes. Staying on an unsupported Node version invites:
- Customer and partner friction: procurement teams increasingly block deployments on runtimes past security support.
- CI drift: base images and package archives stop receiving minimal fixes, creating a slow‑burn reliability issue.
- Incident blast radius: freshly disclosed vulnerabilities in widely used packages can turn into one‑request crashes on old nodes.
Recent advisories reinforce the point. January security releases hardened Node’s permission model and TLS error paths. In early February, a high‑impact DoS in @isaacs/brace-expansion (fixed in 5.0.1) reminded everyone how a tiny parsing edge case can topple a process. If your services process user file patterns, globs, or templated inputs, these aren’t academic concerns—they’re uptime risks.
Primary question: upgrade to Node 24 LTS now, or wait?
Waiting adds risk without benefit. Node 24 LTS is stable, widely adopted in hosting images, and supported to 2028. Upgrading now unblocks dependency updates, simplifies audits, and avoids a future crunch when providers deprecate older runtimes. Migrate to 24 LTS and keep a small canary track ready to adopt the next Current line when you have a performance reason to do so.
The 45‑Day Node.js EOL 2026 Migration Plan
This plan assumes a portfolio of services, 1–3 web backends, and at least one worker or queue consumer. Adjust the scope to your footprint, but keep the week‑by‑week cadence. The goal: zero surprise regressions and a measured rollout to production by Day 45.
Week 1: Inventory and truth‑finding
List every service, function, and worker with its Node version, container base image, and CPU architecture. Capture:
enginesinpackage.json, Node version in Dockerfiles, and CI runners’ Node tooling.- Native modules (
node-gyp,sharp,bcrypt, database drivers) that might rebuild on upgrade. - Traffic tier per service: revenue‑critical, internal, or batch.
Decide the order: internal services first, then read‑heavy APIs, then write‑paths and payment‑adjacent systems. If you deploy on Vercel or another platform with edge/server hybrids, confirm runtime versions per target environment. For feature‑flagged rollouts, our field notes on safer releases can help—see how to ship safer on Vercel using flags and sandbox egress.
Week 2: Local boots and CI green builds
Pin Node 24 LTS locally and in CI. Upgrade TypeScript, ESLint, and test runners to current majors that officially support Node 24. Regenerate lockfiles. If you use pnpm, upgrade to a version that supports node-linker=hoisted or your team’s standard choice with Node 24.
Quick wins this week:
- Upgrade
@isaacs/brace-expansionconsumers. If it’s transitive, bump the parent (e.g., globbing libraries) or add an overrides block to force 5.0.1+. - Run
npm auditor your SCA scanner across both dev and production lockfiles. - Establish a minimum test matrix: Node 22 (if you still support it), 24, and one canary of 25 to spot behavior drift.
Week 3: Runtime parity and performance baselines
Stand up a staging environment on Node 24 LTS that mirrors production shape: same instance sizes, same autoscaling policy, same caches. Recreate realistic traffic: use recorded traces and anonymized payloads. Measure:
- P95/P99 latencies for hot endpoints.
- Connection churn (TLS handshakes per second), keep‑alive reuse, and memory plateaus.
- GC pause times and heap growth after batch jobs.
Set guardrails: “no regression >5% in P95 latency, no increase in error rate.” If you exceed them, profile before reverting—many deltas are dependency‑level or fixed by bumping a single native module.
Week 4: Dark launches, canaries, and progressive exposure
Route 1–5% of production traffic to Node 24 pods behind the same load balancer. Keep the old runtime hot for instant failback. Gate write paths behind a flag and start with idempotent endpoints. Observe saturation behavior during traffic spikes, cache flushes, and deploy rollouts. If your platform supports version locking or skew protection, enable it so old clients hit compatible servers during deploys.
Week 5: Turn the crank
Scale exposure to 25%, then 50% over several days. Remove the write‑path flag once you’ve seen healthy retries, consistent idempotency keys, and stable queue depths. Cut over cron and workers last, then lock the runtime in CI/CD so new merges can’t target old Node versions by accident.
Hidden snags you’ll hit (and how to avoid them)
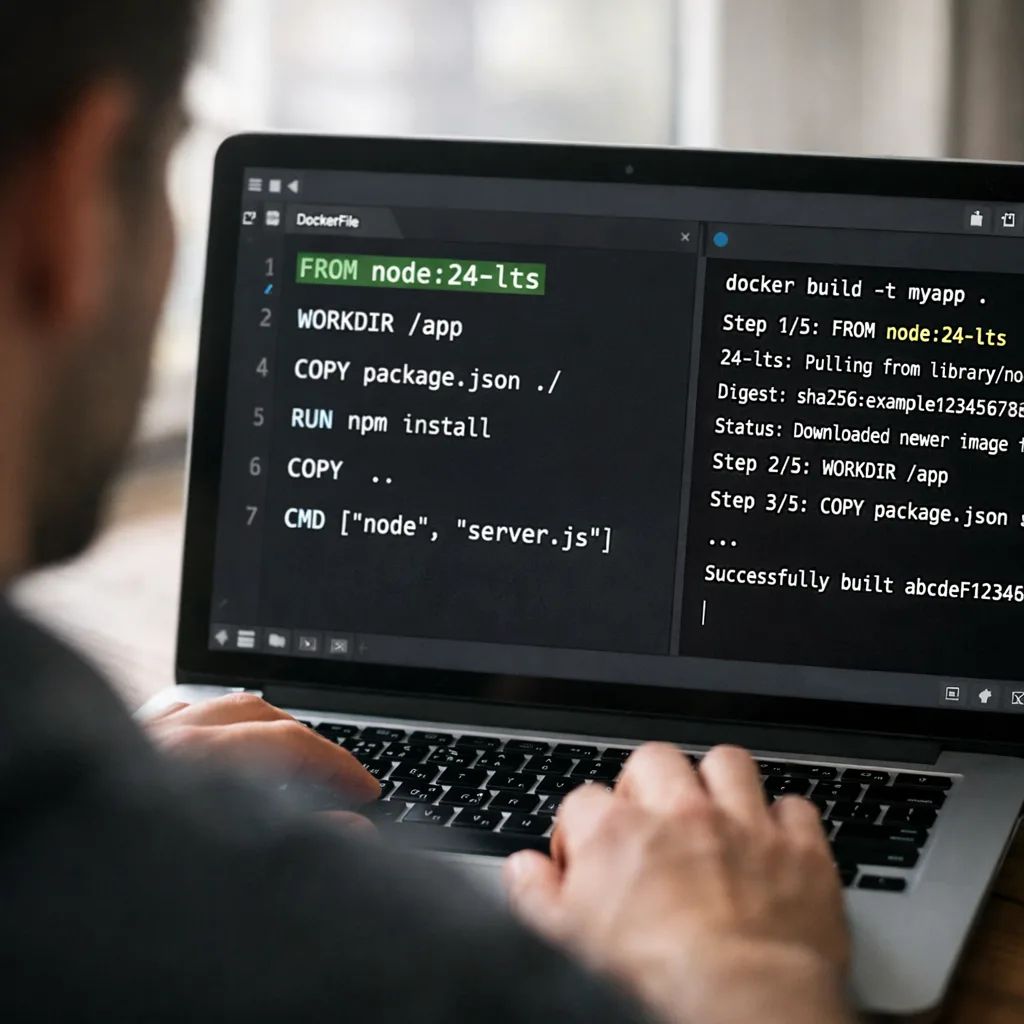
1) “Works on my machine” vs container images
Developers often upgrade local Node quickly but forget base images. Align your Dockerfile (FROM node:24-alpine or your distro base) with CI and staging, then compare node -p process.versions across environments. Mismatched OpenSSL builds, ICU data, or glibc/musl can produce odd TLS or i18n bugs.
2) Native modules and prebuilds
Libraries like sharp, sqlite3, and bcrypt may download prebuilt binaries that lag behind. Force rebuilds in CI (npm rebuild), and cache them for speed. Keep an escape hatch: a separate image layer that pins a known‑good prebuild set while you push vendors for updates.
3) Permission model assumptions
Security releases tightened parts of Node’s permission model and TLS error handling. If you run with experimental permissions, re‑verify that Unix Domain Socket access and symlinked file paths behave as your policies expect. Add explicit error handlers for TLS and HTTP/2 bootstrapping to prevent process crashes from malformed inputs.
4) Transitive dependency risks from globbing and template inputs
Globbing utilities and brace expansion show up everywhere—build scripts, file uploads, template resolvers. Audit inputs that accept patterns from users or other systems. Enforce maximum range sizes, limit nesting, and cap max-old-space-size for worker pools that parse untrusted strings.
People also ask: common upgrade questions
Will I need to recompile native add‑ons?
Plan for it. Most popular packages ship prebuilds, but CI should still run npm rebuild on Node 24. If you maintain internal native code, align your toolchain (Python, make, compiler) with the version used in production images to avoid subtle ABI mismatches.
Is Node 24 LTS fast enough for high‑throughput APIs?
In practice, yes. Focus your performance work on hot loops and serialization. The biggest wins we see are: HTTP keep‑alive tuning, JSON parse/serialize replacement on critical paths, and smarter cache invalidation. If you max out CPU, scale horizontally before micro‑optimizing V8 flags.
What if I’m still on Node 20 after April 30, 2026?
Minimize exposure: segment services behind WAF rules, isolate public endpoints, and shorten session lifetimes. Freeze deploys to security fixes only, and fast‑track the Node 24 migration with a dedicated strike team. Every week past that date increases the attack surface and audit risk.
The Node 24 Readiness Checklist
Use this as a pre‑cutover gate for each service:
- Runtime pinned: Node 24 in
engines, Dockerfile, and CI. - Lockfile refreshed and vulnerability scan clean on both prod and dev dependencies.
- Native modules rebuilt and cached; image size growth understood.
- Security posture verified: TLS error handlers attached; file permission and socket access aligned with policy.
- Observability in place: CPU, heap, GC, P95/P99, and error sampling dashboards compared to baseline.
- Rollout toggles ready: feature flags, skew/version locking, and 1‑click failback.
Service‑by‑service upgrade framework
Here’s a simple scoring model to prioritize the order of migration:
- Business criticality (0–5): revenue adjacency and SLA tier.
- Complexity (0–5): native modules, external integrations, data write patterns.
- Blast radius (0–5): fan‑out to other services, queue depth, customer impact.
Migrate low‑criticality + high‑complexity services early to flush issues without risking revenue, then tackle high‑criticality systems once the path is proven. Track scores in a visible doc and review daily during rollout.
Security to‑dos tied to current advisories
Make these changes part of your sprint, not backlog items:
- Force
@isaacs/brace-expansionto^5.0.1or later via overrides/resolutions, and cap pattern inputs from users. - Re‑run your test suite with malformed HTTP/2 and TLS handshakes to ensure errors don’t crash the process; attach explicit socket error handlers.
- Enable rate limits on endpoints that parse user‑controlled strings (uploads, search, import jobs) and set timeouts so expensive work can’t starve the event loop.
Operational playbook: rollouts that don’t wake up the on‑call
Keep deploys boring:
- Blue/green with skew protection: route a sliver of traffic to Node 24 pods; keep old pods warm for instant failback.
- Experiment flags, not config flips: ship flags per endpoint or pathway to unwind quickly without redeploying.
- Slow bake windows: promote from 5% to 25% to 50% during local business hours so SREs can watch graphs and logs.
If your team wants help pressure‑testing this strategy, our technical delivery approach and platform services cover canary strategies, performance baselining, and incident drills. You can also browse our recent platform migrations to see how we de‑risk upgrades for complex stacks.
People also ask: do we need to touch frontends?
If you’re on a full‑stack framework like Next.js, you’ll feel this change in server components, route handlers, and build tooling. Align your Node version in:
- Local dev (Volta/nvm + lockfiles) and CI runners.
- Edge versus server runtimes (confirm supported versions per target).
- Build cache and ISR/SSR caches—clear and repopulate to avoid stale serialization artifacts.
What to do next (today)
- Create a single runtime matrix and pin Node 24 in CI, Dockerfiles, and
engines. - Open an org‑wide issue: "EOL 2026" with the inventory and service scores.
- Stand up a Node 24 staging that mirrors production and record baselines.
- Schedule a 5% canary by the end of next week; book a rollback drill on the same calendar invite.
- Close the loop with a post‑cutover review: perf diffs, error classes, and dependency follow‑ups.
If you want more release management tactics and migration playbooks, our engineering blog and recent migration guides are built for teams like yours.

Final take
Deadlines focus the mind. Node.js EOL 2026 isn’t a future‑you problem; it’s a near‑term delivery milestone. Move to Node 24 LTS now, measure what matters, and roll out with canaries and version locking. Do that, and the dates on the calendar become just another routine release—not a 2 a.m. incident.




Comments
Be the first to comment.