Third‑Party Cookies Are Staying. Now What?
Let’s get straight to it: third‑party cookies are still in Chrome, and they’re not being forcibly removed right now. That means the near‑term reality for growth teams and engineers is a mixed bag—some breathing room, but zero excuse to pause modernization of measurement and privacy. If you’ve been waiting for a hard cutoff, you won’t get one. Plan for continuity with third‑party cookies while building durable, first‑party paths that won’t crack under the next policy turn.
Back on April 22, 2025, Google said it would maintain its existing approach to third‑party cookie choice in Chrome and wouldn’t roll out a new one‑click opt‑out prompt; multiple outlets reported the pivot and quoted Google’s Privacy Sandbox VP by name. (engadget.com)
Regulatory pressure helped shape that path. The UK CMA later released Google from enforceable Privacy Sandbox commitments on Oct 17, 2025, after a multi‑year process—effectively clearing the way for a lighter‑touch, market‑led transition. (gov.uk)
Meanwhile, some Sandbox pieces remain technically available. Chrome’s documentation notes that Protected Audience API event‑level win reporting will be supported until at least 2026, and a fence‑frame mandate won’t kick in before 2026 either. Translation: experimentation continues even if the “no‑cookies world” isn’t here. (privacysandbox.google.com)
Why this matters even if third‑party cookies keep working
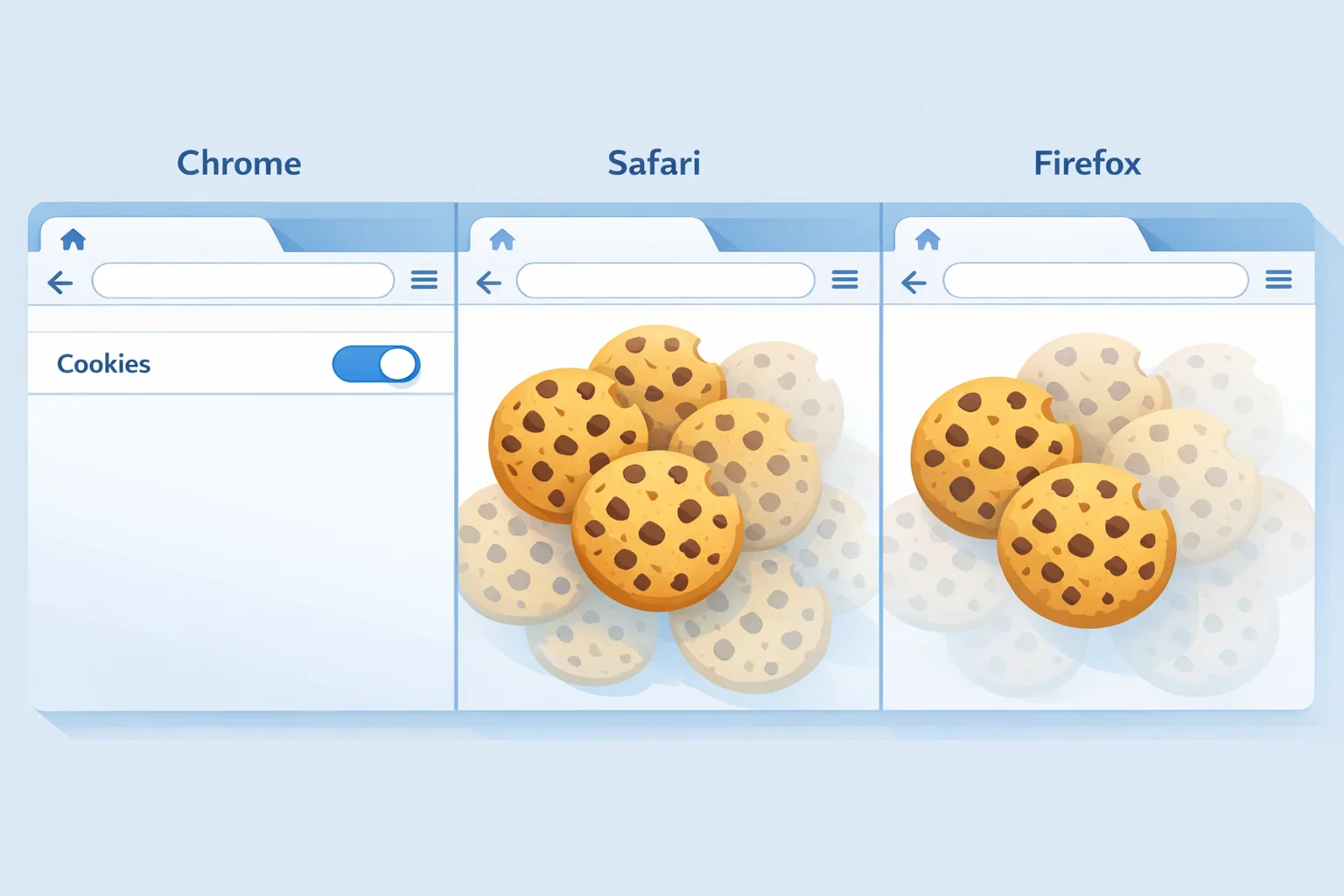
Here’s the thing: Chrome’s dominance means any directional change—delay, pivot, or policy tweak—reverberates across how we attribute conversions, control frequency, and reconcile revenue. Even with cookies in play, measurement is noisier thanks to ITP/ETP elsewhere, consent gating, anti‑tracking extensions, and app platform shifts. Chrome’s still the heavyweight, so keeping your stack Chrome‑ready is table stakes; making it cookie‑resilient is the differentiator. (pcworld.com)
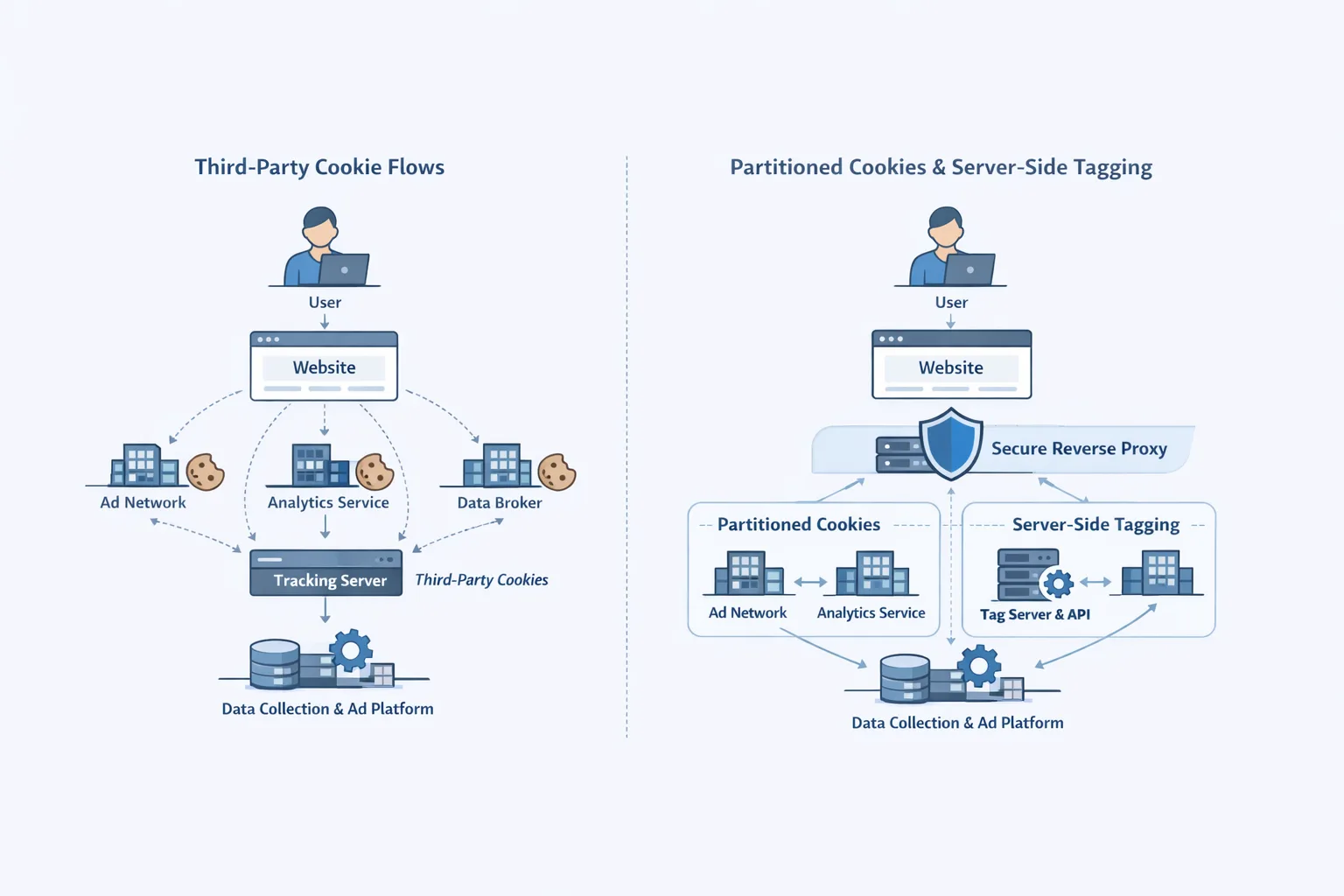
If you’re a marketer or product owner, assume a hybrid future: cookies where available, consented first‑party IDs where possible, and API‑based attribution for gaps. Engineering has to stitch those paths cleanly or you’ll be debugging phantom losses and over‑counted wins all quarter.
The 2026 playbook for third‑party cookies (and beyond)
The priority is to make today’s performance dependable while you de‑risk tomorrow. Use this two‑lane approach: optimize what still works; harden what will outlast policy flips.
Lane A: Stabilize what still runs on third‑party cookies
Keep the lights on without digging the hole deeper.
- Inventory dependencies. Map every tag, pixel, and SDK that writes or reads third‑party cookies. Classify by purpose: conversion, frequency capping, fraud, personalization, and “unknown/legacy.”
- Minimize cookie sprawl. Consolidate redundant tags and sunset zombie pixels. If you can’t explain a cookie’s job in one sentence, it’s a risk.
- Use consent APIs consistently. Wire consent state into your tag manager and ad platform templates so behavior is deterministic across pages and apps.
- Isolate breakage gracefully. For flows that truly need third‑party cookies (e.g., legacy remarketing), build safe fallbacks—URL parameters, server hints, or signed first‑party tokens where policy allows.
Lane B: Build durable, privacy‑forward measurement
Cookies are convenient; durability is strategic. Focus here:
- First‑party data model. Design an event and identity schema that covers visitors, accounts, and devices with explicit consent and retention windows. This is your highest‑leverage asset.
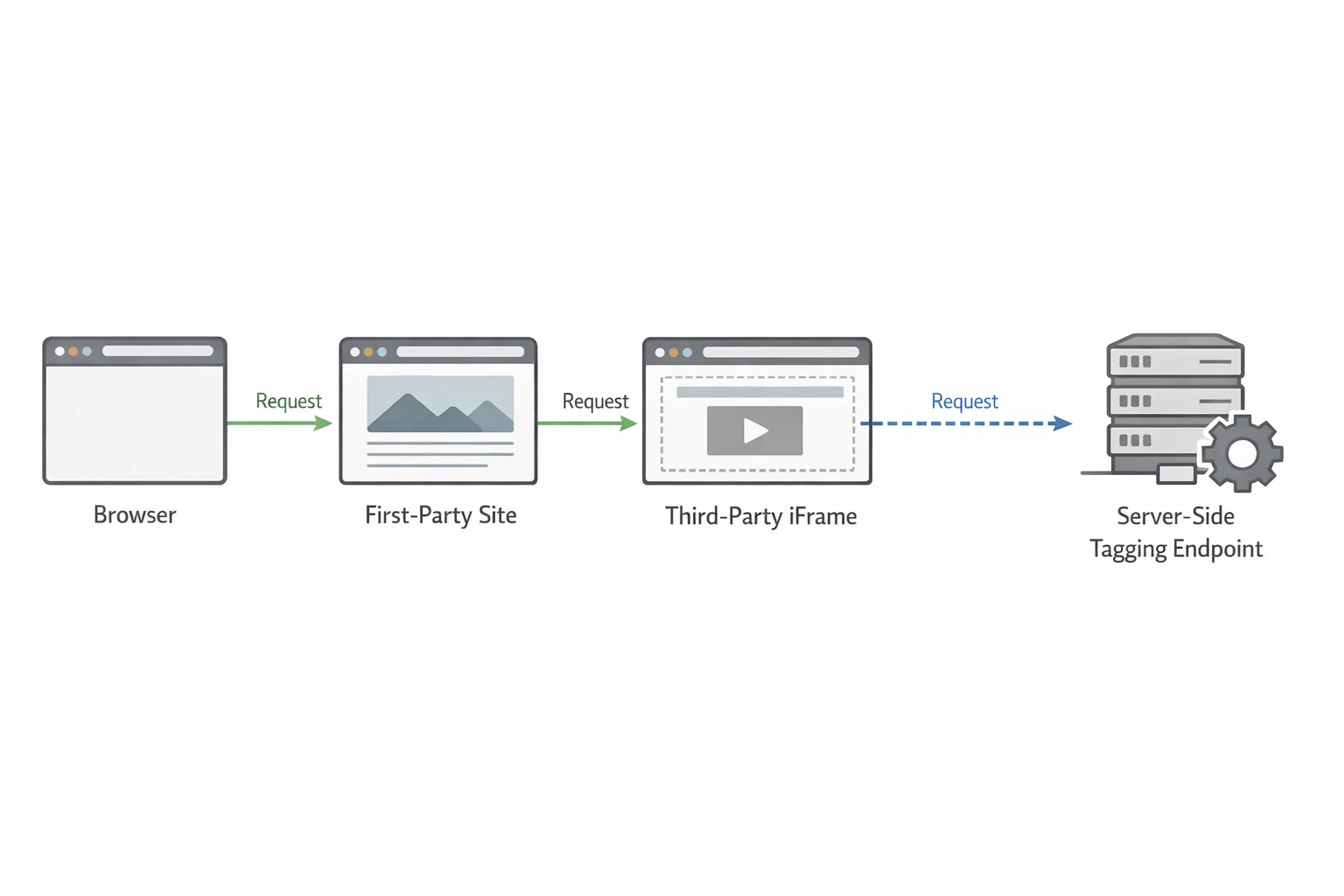
- Server‑side tagging (SST). Move collection to your domain on your infra (or a trusted managed endpoint). You’ll cut client overhead, reduce ad‑block fragility, and centralize governance.
- Attribution APIs. Test Chrome’s Attribution Reporting API (ARA) and measurement flows where relevant; they’ll coexist with cookies and smooth over loss in stricter browsers. (privacysandbox.google.com)
- Protected Audience experiments. If you run remarketing at scale, pilot PAAPI in low‑risk slices while cookies still backstop performance; event‑level win reporting remains supported into 2026. (privacysandbox.google.com)
- Data clean rooms. For high‑budget media, use clean rooms to compare cohort‑level lift and reduce reliance on raw user joins.
FAQ: Do third‑party cookies still work in Chrome?
Yes. As of February 20, 2026, Chrome hasn’t removed third‑party cookies by default and isn’t rolling out a new universal prompt to shut them off. Users can still manage cookie settings manually. That’s per Google’s April 22, 2025 update. (engadget.com)
FAQ: Is the Privacy Sandbox “dead,” and does it matter?
Reports in late 2025 said Google scaled back or rebranded parts of Privacy Sandbox, and the UK CMA formally released its oversight commitments. Practically, some APIs remain documented and testable (e.g., PAAPI and ARA), but the “hard stop” narrative is off the table. Treat Sandbox tech as optional accelerants—not the single point of failure. (gov.uk)
Design a durable measurement stack: the Five‑R Framework
Use this to pressure‑test your plan in a one‑day workshop.
- Results: Define the business outcomes you must measure (revenue, ROAS, LTV, CAC payback) and the confidence interval you’ll accept by channel.
- Records: Map events, identities, and consent across web, iOS, Android. Document legal bases and retention windows.
- Routing: Decide what fires client‑side vs server‑side. For SST, pick a region, CDN strategy, and security posture (WAF, mTLS, tokenization).
- Reconciliation: Choose how you unify conversions—cookies where available, ARA/PAAPI for gaps, offline CRM matches via clean rooms.
- Resilience: Simulate failure modes (cookies blocked, consent withdrawn, SDK outage) and ensure graceful degradation with monitoring and alerts.
Data‑backed checkpoints to anchor 2026 planning
What’s verifiably true and useful to plan around right now?
- April 22, 2025: Google said it will keep the current approach to third‑party cookie choice in Chrome and won’t ship a new prompt. (engadget.com)
- October 17, 2025: The UK CMA released Google from the binding Sandbox commitments after consultation. (gov.uk)
- 2026: Chrome’s docs still state Protected Audience event‑level reporting is supported until at least 2026; fenced frames won’t be mandated before 2026. (privacysandbox.google.com)
- Chrome continues to dominate browser usage globally, so optimization for Chrome has outsized impact on measurement quality. (pcworld.com)
Let’s get practical: a 90‑day upgrade plan
Days 1–15: Audit and align
Kick off a cross‑functional audit. Inventory tags, pixels, and SDKs; map consent flows; and document every place a third‑party cookie is read or written. Create an issue list with owners, risk, and ROI. Parallel‑path a simple KPI baseline for the next 90 days so you can attribute gains to this work—not seasonal changes.
Days 16–45: Ship server‑side tagging and consent hardening
Stand up a server‑side tag endpoint on your first‑party domain with rate limiting and WAF rules. Route high‑volume conversion and remarketing tags server‑side, preserving consent signals end‑to‑end. Add circuit breakers so a vendor outage won’t tank page performance. Measure page weight and TTFB deltas pre/post; SST usually pays back in both stability and speed.
Days 46–75: First‑party identity and API measurement
Roll out a hashed, first‑party identity keyed to authenticated sessions or high‑intent actions, with explicit consent and TTLs. Light up ARA testing for at least one major campaign, and run a split where possible: cookie vs cookie+API. If you operate at retargeting scale, pilot a Protected Audience test slice while cookies remain your safety net. (privacysandbox.google.com)
Days 76–90: Validation and governance
Close with a measurement council review: marketing, data, security, and legal. Freeze a change log, finalize a runbook for incident response (broken attribution, consent mis‑wires), and write owner‑friendly documentation so nothing atrophies when people rotate.
Risks and tradeoffs you should acknowledge to your execs
Server‑side tagging isn’t a magic shield. You must pass consent and lawful basis transparently, and you still own vendor due diligence. If you proxy requests sloppily, you can break vendor terms or misattribute conversions. Protected Audience and Attribution Reporting add operational complexity; the benefit comes from resilience and signal quality, not instant CPA drops. And any privacy incident will cost far more than the incremental revenue from aggressive tracking. Say this out loud in your plan.
What about Safari, Firefox, and apps?
Even if Chrome keeps cookies, WebKit’s ITP and Firefox’s ETP continue to curtail cross‑site tracking by default, and app ecosystems have their own consent regimes. That’s why the first‑party stack and SST bring leverage beyond Chrome. Treat cookie availability as a best‑effort bonus, not a design requirement.
How to explain this to stakeholders (without hand‑waving)
Use a simple narrative: “Cookies still function in Chrome today, but our growth depends on signals we control. We’re moving collection first‑party, enforcing consent, and adopting APIs that keep attribution stable across browsers. That saves engineering hours, ads dollars, and legal risk.” Then show the next 90 days of commits and expected deltas.
When to double down on Sandbox‑style APIs
Two scenarios justify more investment: heavy remarketing exposure (you need a future alternative to frequency and audience joins) and high spend where incrementality confidence drives budget. In both cases, carve out controlled experiments now while the cookie backstop lets you learn without wrecking ROAS. Keep an eye on Chrome platform notes for any 2026 policy changes. (privacysandbox.google.com)
People also ask
Will Chrome ever remove third‑party cookies?
There’s no committed date. Google’s April 2025 decision explicitly paused both removal and a new prompt; expect incremental privacy features instead of a cliff. Plan accordingly, test APIs, and avoid new hard dependencies. (engadget.com)
Do I still need server‑side tagging if cookies stay?
Yes. SST reduces client breakage, centralizes governance, and keeps you adaptable if browsers change course again. It’s as much a reliability and security investment as it is a privacy one.
Is Protected Audience worth testing?
If remarketing is material to your mix, yes—run measured pilots. Event‑level win reporting is supported into 2026, giving you time to learn without betting the farm. (privacysandbox.google.com)
What to do next
- Book a half‑day audit to map cookie dependencies and consent wiring.
- Stand up server‑side tagging on your domain with basic WAF and rate limits.
- Pilot Attribution Reporting and one Protected Audience test while cookies backstop performance. (privacysandbox.google.com)
- Publish a measurement runbook and escalation matrix that product, data, and marketing can live with.
If you’d like experienced hands to accelerate this work, here’s what we do for growth and engineering teams, a look at our client results and implementations, the services we recommend for durable analytics, and where to reach us to scope a 90‑day plan.



Comments
Be the first to comment.