Third‑Party Cookies in Chrome: The 2026 Playbook
Let’s get straight to it: third‑party cookies in Chrome are still here, and Chrome 144 is now deprecating several Privacy Sandbox APIs that were meant to replace them. If your analytics and ad stack slowed rollouts waiting for the cookie sunset, you need a new plan—one that embraces durable first‑party measurement while remaining compatible with Chrome’s present reality and Safari/Firefox’s stricter defaults.

What just changed (and when)
Here’s the short version, with the dates that matter for roadmaps and Q1/Q2 planning.
• On April 22, 2025, Google confirmed it would maintain user choice for cookies in Chrome rather than removing third‑party cookies or adding a new prompt. That set the policy direction for the near term.
• On October 17, 2025, the UK’s CMA released Google from the legally binding Privacy Sandbox commitments tied to cookie deprecation, a strong external signal that the original deprecation pathway was off the table.
• On January 13, 2026, Chrome 144 landed on Stable. Its release notes include planned deprecations/removals for multiple Sandbox pieces—specifically Private Aggregation, Shared Storage, and Protected Audience—reflecting a broader wind‑down of the web APIs that were designed for a cookie‑less Chrome.
• On Android, Google’s developer documentation now marks “Privacy Sandbox on Android” as deprecated (as of October 17, 2025). If you experimented with Topics or Attribution Reporting on Android, plan to unwind those code paths.
What does that mean in practice? If you were betting on Topics, Protected Audience, or Shared Storage becoming the backbone of your web advertising and measurement, that bet won’t pay out. Chrome is moving away from those Sandbox APIs while keeping third‑party cookies available under user control. Your stack should move accordingly.
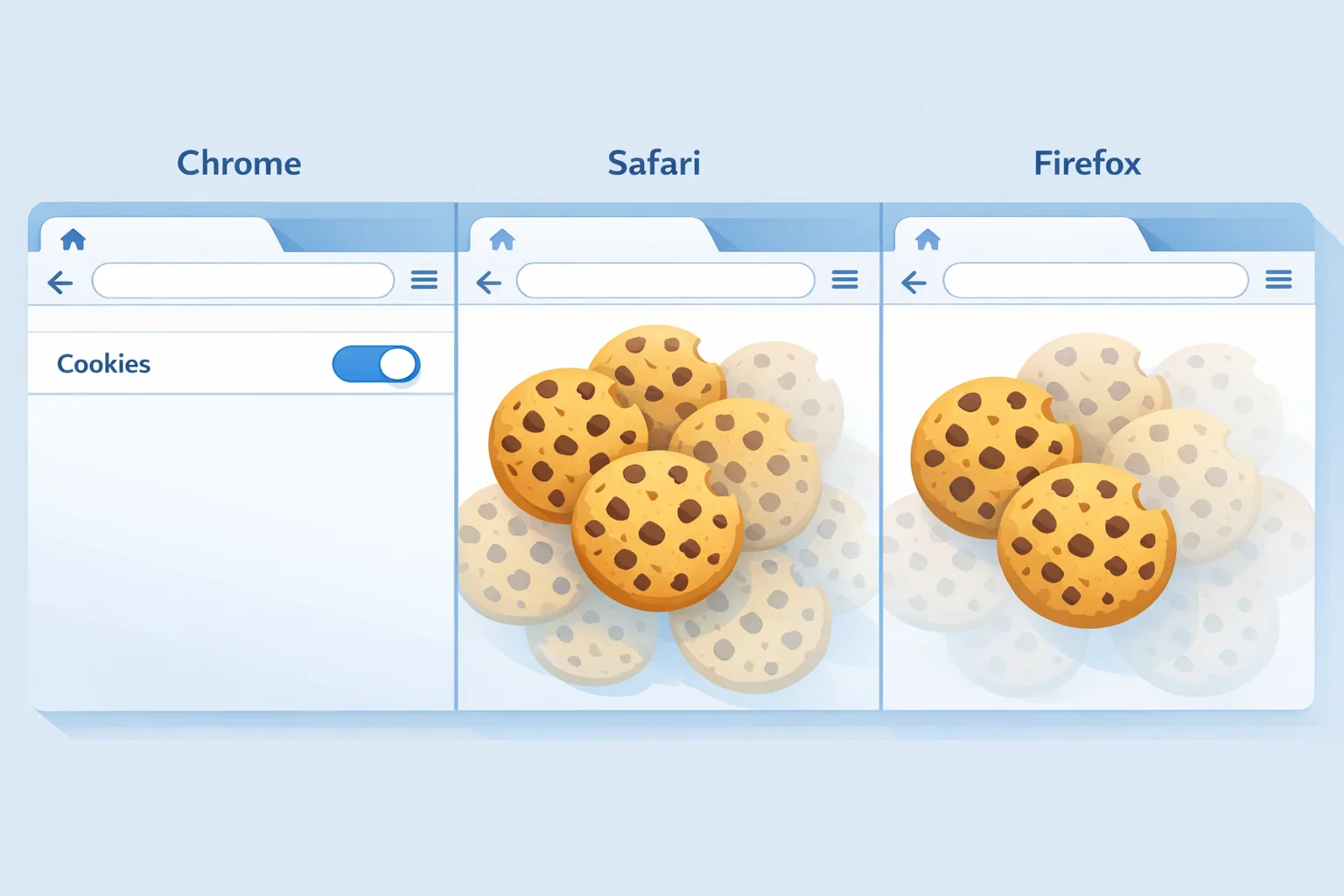
Third‑party cookies in Chrome: should you rely on them again?
Yes—and no. Yes, in the sense that Chrome will continue to send third‑party cookies unless the user blocks them or you set things up incorrectly. Your advertising and analytics can keep functioning there. But no, in the sense that leaning solely on third‑party cookies is a brittle strategy in 2026. Safari and Firefox continue to restrict third‑party cookies, and regulators expect purpose limitation, minimization, and true consent. If you rebuild like it’s 2018, you’ll get uneven performance by browser and risk compliance issues.
Here’s the thing: durable measurement today is a layered approach. Chrome’s posture buys you time, not immunity. The winners are the teams that modernize their first‑party data, consent, and server‑side measurement while keeping Chrome‑specific fallbacks for near‑term performance.
The durable signal stack for 2026
Use this opinionated stack as your baseline. It preserves performance in Chrome while giving you cross‑browser resilience.
1) First‑party identity and consent
• Adopt a consistent, privacy‑aware first‑party identifier (hashed user ID or stable anonymous device/browser key) scoped to your domain(s). Make sure you rotate and expire appropriately.
• Implement a high‑quality Consent Management Platform (CMP) with region logic and granular toggles. Wire consent states into your data layer so tags and server endpoints can honor them deterministically.
• Align with current frameworks (e.g., IAB TCF in the EU) and keep audit trails. Many “measurement gaps” are actually consent wiring gaps.
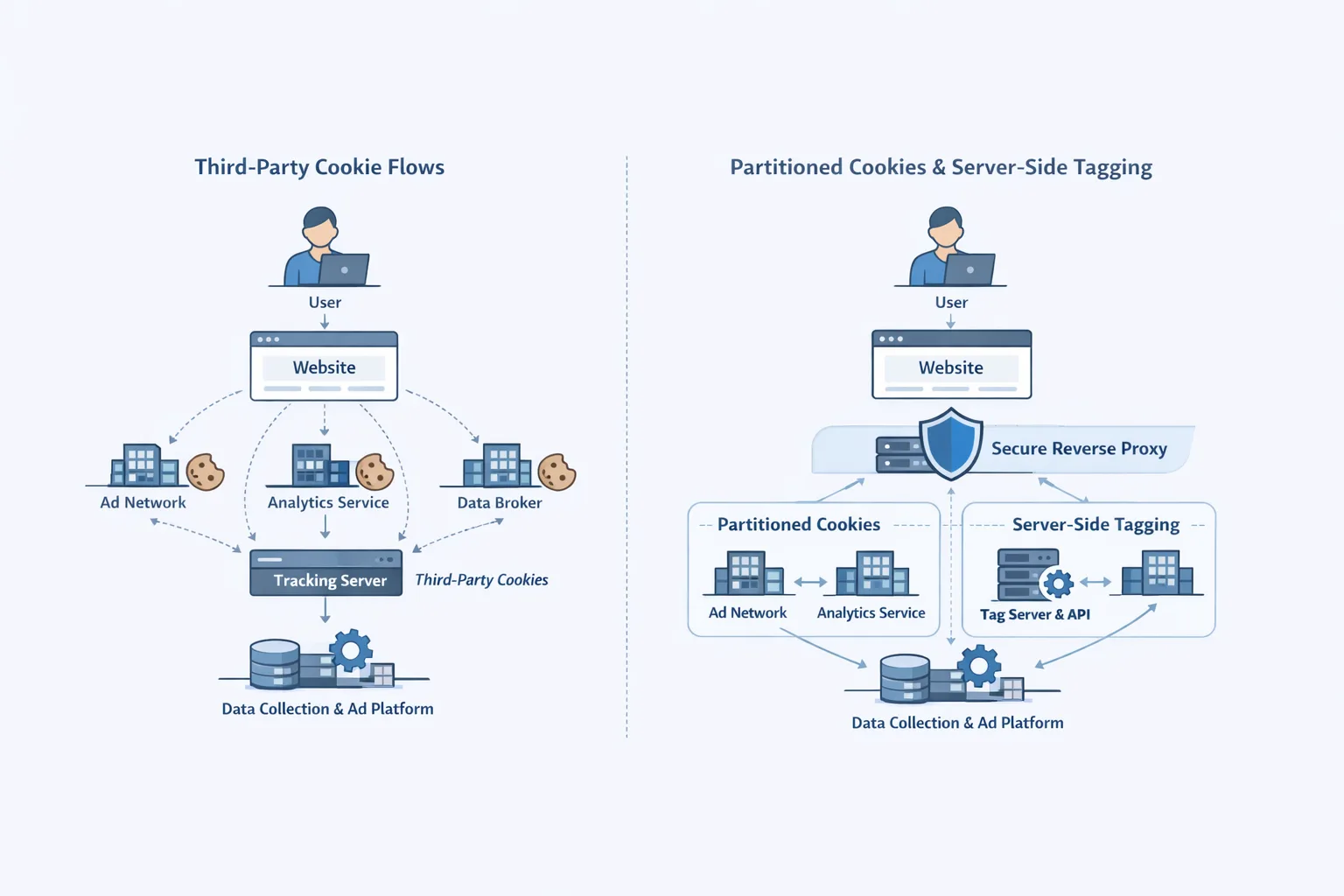
2) Server‑side tagging and event pipelines
• Move browser events into a server‑side tag gateway you control. This lets you normalize payloads, apply consent gating, and attach first‑party identifiers consistently.
• Use signed requests and schema validation. Do not forward raw client payloads to ad platforms.
• Maintain per‑destination allowlists so you can shut off a partner cleanly if policy or performance changes.
3) Cookie hygiene and SameSite settings
• Audit every cookie your site sets. Ensure Secure, HttpOnly (where applicable), and accurate SameSite attributes. Breakage often comes from lax cookie flags, not policy shifts.
• Where you truly need third‑party storage across sub‑domains or vendors, map those dependencies and build first‑party alternatives where possible.
4) Cross‑browser measurement strategy
• Chrome: continue to collect conversions via third‑party and first‑party cookies, gated by consent.
• Safari/Firefox: expect third‑party blocking; lean on first‑party cookies, server‑side tagging, and modeled conversions (with documented assumptions). Keep UX fast and consent transparent to preserve opt‑ins.
5) Modeling with integrity
• Where platforms provide modeled conversions, document the inputs you send and the guardrails (minimum volumes, lookback windows). Treat modeled numbers as estimates with confidence intervals for decision‑making, not exact truth.
If you tested Privacy Sandbox APIs, unwind safely
Some teams shipped experiments with Protected Audience auctions, Topics, Shared Storage, or Private Aggregation. With Chrome 144 signaling deprecation/removal and the feature status page marking more Sandbox pieces as “intent to deprecate,” treat this like a normal feature sunset.
• Identify code paths and experiment flags referencing Sandbox APIs. Search for permissions policies like join-ad-interest-group, run-ad-auction, and fenced‑frame usage.
• Remove or stub calls that will start failing as APIs disappear. Keep a feature flag in case schedules shift, but do not keep dead code in production builds.
• Shift remarketing off interest group auctions to your existing first‑party audiences and traditional platform pixels (with consent). Expect some CPA/CAC changes; mitigate with creative testing and landing‑page speed improvements.
• If you stored data solely for Sandbox flows (e.g., key/value services for auctions), plan your archival or deletion schedule so you don’t carry technical and compliance debt.
People also ask: Will Chrome reverse course again?
There’s no public plan to deprecate third‑party cookies in 2026. The documented direction since April 2025 is to maintain user choice and back away from the Sandbox‑as‑replacement track. Could policy change in the future? Sure, but today’s prudent posture is to ship a stack that works with or without third‑party cookies, not to wait for another big swing.
People also ask: What replaces Protected Audience and Topics?
Nothing one‑for‑one. In Chrome, the immediate replacement is the status quo—third‑party cookies plus your first‑party dataset. Across all browsers, the pragmatic replacement is a stronger first‑party strategy: audiences built from consented site signals, contextual targeting, and modeled measurement routed through server‑side endpoints. That’s not as novel as the Sandbox vision, but it’s practical and shippable now.
Data points to anchor your plan
• Chrome 144 released to stable on January 13, 2026, with deprecation/removal notes for Private Aggregation, Shared Storage, and Protected Audience. This is your near‑term engineering trigger.
• Google’s Android docs mark “Privacy Sandbox on Android” deprecated as of October 17, 2025; do not invest fresh effort there unless guidance changes.
• The UK CMA’s October 17, 2025 decision to release Sandbox commitments reduced regulatory pressure on Chrome’s deprecation path. Treat this as a medium‑term stabilizer rather than a permanent guarantee.
These dates aren’t trivia; they’re the calendar anchors you should include in Jira tickets and QBR decks.
Checklist: ship this in the next 30 days
Use this as a stand‑up driver with product, growth, and engineering.
1) Cookie inventory and flags: Generate a full list of cookies set on your site, by host and path, with name, purpose, lifetime, and SameSite/HttpOnly/Secure attributes. Fix mis‑flagged cookies and shorten lifetimes where you can.
2) CMP wiring: Verify your CMP fires before any data‑collecting tag. Ensure the consent state is in your data layer and propagated to your server‑side tag gateway. Test from EU, CA, and US regions with a VPN.
3) Server‑side tagging: If you’ve parked this, stand up a minimal gateway for your top three destinations (analytics, ads platform A, ads platform B). Route high‑value events first (purchase, signup). Log rejections when consent is missing.
4) Chrome 144 audit: Run a crawl and a few happy‑path user flows with DevTools open. Note deprecation warnings for Sandbox calls. Remove Protected Audience, Shared Storage, and Private Aggregation code paths and feature flags.
5) Cross‑browser test: Validate conversion flows on Safari and Firefox with third‑party cookies disabled. Fix any dependencies on third‑party storage you didn’t realize you had.
6) Creative and landing‑page tune‑up: Expect some campaign turbulence as you rebalance audiences. Offset with faster pages and better above‑the‑fold messaging. Our React 19 migration checklist includes practical performance wins.
7) Platform upgrades: Keep your ad APIs and SDKs fresh. 2026 versions are rolling; upgrading early avoids forced sunsets during peak seasons.
Engineering notes: cookies, storage, and headers
• SameSite=Lax is the browser default for host cookies; if you depend on cross‑site requests for auth or tracking, you’ll need SameSite=None; Secure (and TLS everywhere). Misconfigured cookies routinely cause “mysterious” conversion drop‑off.
• Storage partitioning continues across engines; don’t assume a shared bucket. Design for first‑party scope and idempotent events.
• Avoid fragile workarounds like fingerprinting. Aside from being ethically dubious, it’s increasingly detectable and can get your domains penalized by platforms.
• Keep your deprecation radar up. Chrome is also removing long‑standing web behaviors unrelated to ads—like the gradual deprecation of the unload event and (later in 2026) XSLT removal. When you plan refactors, bundle these with your privacy work to cut regression risk.
People also ask: Do we still need a CMP if Chrome keeps cookies?
Absolutely. Consent isn’t a browser toggle; it’s a contract with users. Beyond EU/UK, multiple US states enforce consent and data rights, and platforms increasingly require consent signals for modeling features. Your CMP is how you prove intent and control processing—cookies or not.
How this impacts SEO and growth teams
• Attribution clarity: With Chrome continuing third‑party cookies, last‑click and multi‑touch models in ad platforms will look “healthier” than Safari/Firefox. Don’t mistake that for universal truth—keep a blended reporting view that weights traffic by browser share.
• Content and performance: If you trim heavy client‑side tag logic and move to server‑side routing, your Core Web Vitals often improve. That’s a rare win‑win: better UX signals for organic search and more resilient measurement.
• Governance: Document your signals, consent states, and partner list. When auditors (or platform reviewers) ask, you’ll have a tidy map instead of a fire drill. If you need help formalizing this, our team outlines deliverables on services and implementation, and you can explore relevant case work on our portfolio.

Risk and compliance: keep it boring (on purpose)
• Data minimization: Collect what you can defend. Tie every field to a purpose. If you can derive it on the server, don’t ship it from the browser.
• Regional behavior: Respect regional toggles. For example, don’t rely on IP geolocation alone; use explicit region choices when possible and cache consent state server‑side.
• Vendor discipline: Maintain a quarterly review of pixels and destinations. Remove vendors that don’t provide clear data‑processing terms or can’t disclose sub‑processors.
• Incident readiness: Log consent state and event forwarding decisions. When a user requests deletion or an authority asks questions, evidence beats scrambling.
What to do next
• Rebase your roadmap on the durable signal stack above. Treat third‑party cookies in Chrome as a helpful bridge, not a foundation.
• Remove Sandbox API dependencies flagged by Chrome 144. Keep a clean, first‑party–centric codebase and server‑side routes.
• Tighten consent and cookie hygiene, then measure the lift in site speed and conversion. If you need a partner to accelerate this, see what we do and reach out via contact.
• Keep an eye on platform release notes each month. Our security ops clients pair this with regular patch cycles—if that’s you, our notes on January 2026 Patch Tuesday show how to prioritize fixes without slowing growth work.

Zooming out
The ad industry spent years preparing for third‑party cookies to disappear from Chrome. That future didn’t arrive. But the teams who did the hard work—improving consent, building server‑side pipelines, cleaning up cookies, and testing across browsers—are in a better position anyway. They run faster sites, have clearer data contracts, and rely less on duct‑taped pixels.
Use this moment to simplify. Ship what’s durable. And make your measurement boring, predictable, and provable—so your team can spend more time on product and creative, not chasing the next privacy plot twist.
If you want a second set of hands to audit your stack or stand up server‑side tagging without burning sprints, we’ve done this for growth teams and engineering orgs across B2C and B2B. Start with a quick scoping call via our contact page.



Comments
Be the first to comment.