App Store Age Verification in 2026: Ship Smart
App Store age verification just moved from “someday” to a roadmap item your team has to actually ship. Texas’ SB 2420 was blocked by a federal judge on December 23, 2025, and Apple paused state‑specific changes the next day, but the story isn’t over—and Utah and Louisiana are scheduled next. Build the implementation once, test it properly, and you’ll be ready when enforcement restarts or expands. (macrumors.com)

Why plan now if Texas is on hold?
Here’s the thing: injunctions shift schedules, not direction. The Texas injunction could be appealed, new bills keep surfacing, and platform tooling is already here. Apple has shipped a privacy‑respecting Declared Age Range signal for apps, and Google Play has a beta Age Signals API with parental approval workflows tied to “significant changes.” Shipping now de‑risks your funnel and avoids a scramble when timelines flip from “someday” to “yesterday.” (developer.apple.com)
What exactly changed for 2026?
Two practical shifts matter to teams:
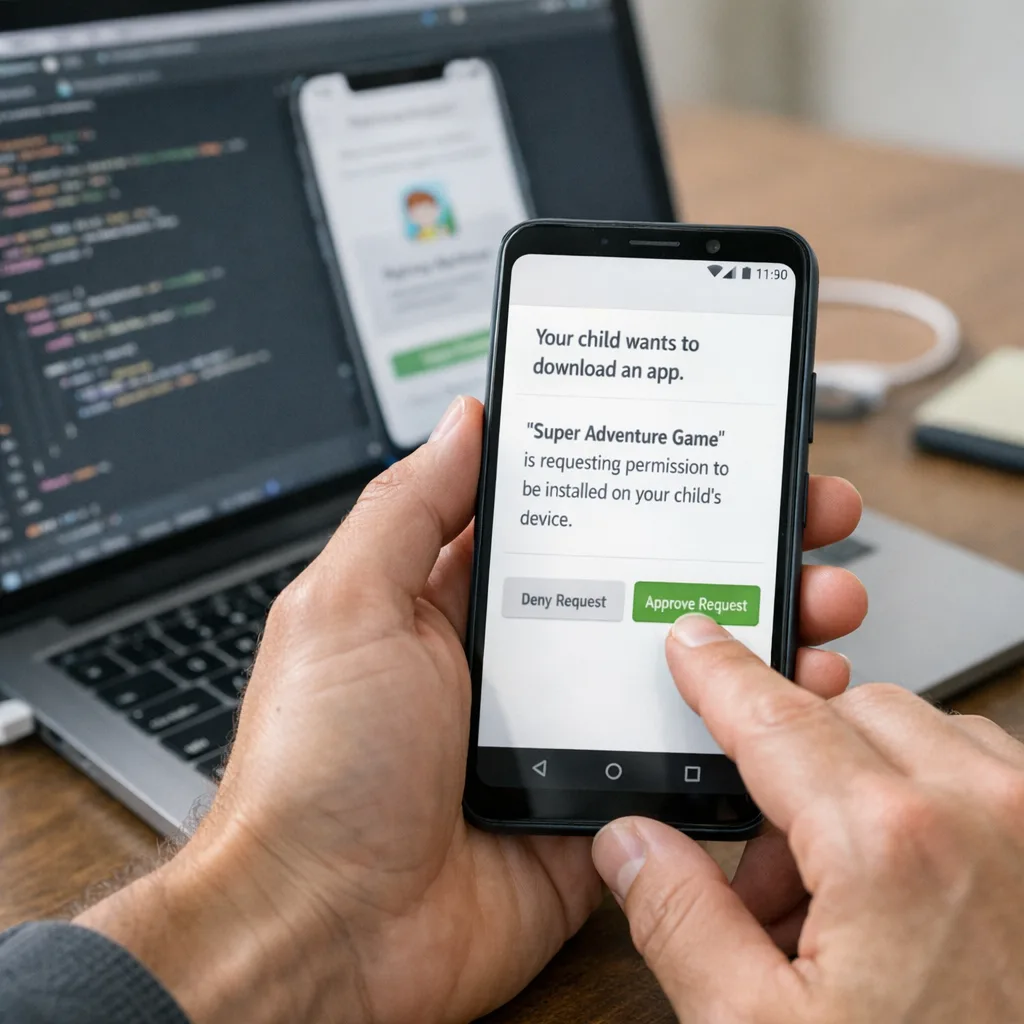
First, Apple and Google prepared developer pathways for age assurance that don’t force you to collect IDs. On iOS, you’ll request an age range (not a birthdate). On Android, you’ll fetch Play’s verification/supervision status and an age band when required by local law. Second, certain states are introducing parental consent requirements for “significant changes,” which means your product updates can trigger a store‑level approval flow for supervised accounts. (developer.apple.com)
Zooming out, Utah and Louisiana are slated for mid‑2026 start dates (subject to litigation and rulemaking), so the window to implement without heroics is right now. (arstechnica.com)
The practical architecture: one implementation, two platforms
Let’s get practical. Your job is to identify a user’s age status, apply the right experience, and honor parental approvals—without storing more data than you need.
iOS: Declared Age Range in the flow
Apple’s Declared Age Range provides an age band like Under 13, 13–15, 16–17, or 18+. You request it early (first launch, gated features, checkout) and adapt UX accordingly. You don’t get a date of birth, and you shouldn’t try to back into one. That’s the point: reduce risk while delivering age‑appropriate experiences. (developer.apple.com)
Gotchas we’ve seen in production: don’t cache the signal indefinitely—treat it like any other account attribute that can change. If you store it server‑side for feature flags, persist only the band, not raw identifiers. And gate entitlements server‑side when money is involved.
Android: Play Age Signals and “significant change” approvals
Google Play’s Age Signals API (beta) returns a userStatus (for example, VERIFIED, SUPERVISED, SUPERVISED_APPROVAL_PENDING) plus an age band when applicable. It also gives you an install ID to correlate revoked approvals, and Play Console lets you declare “significant changes” with an effective date so parents can approve or deny. (developer.android.com)
Pro tip: pair Age Signals with Play Integrity so your server trusts the signal’s origin. Don’t roll your own cryptography or accept self‑reported client state without verification.
Is App Store age verification mandatory today?
In Texas, a federal preliminary injunction stopped SB 2420 from taking effect on January 1, 2026, and Apple paused enforcement plans while keeping dev tools available for testing. That pause isn’t a permanent pass; the case can be appealed, and other states are advancing similar requirements. (macrumors.com)
Framework: AGERAIL for shipping age‑aware apps
Use this seven‑step checklist to move from “we’ll figure it out” to “we shipped it.”
- Assess: Inventory surfaces where age matters—signup, content discovery, UGC, ads, analytics, payments, and support.
- Gate: Define experience by age bands. What’s blocked, what’s visible, and what’s default‑off for 13–15 vs. 16–17?
- Entitlements: Tie monetization to verified adult or supervisor‑approved flows; map each SKU/feature to required status.
- Re‑consent: Decide what constitutes a “significant change” (price model, data use, new social features). Plan how you’ll trigger parental approval on Android and re‑permission on iOS if required by law.
- Audit: Minimize data. Don’t store IDs; store the minimum band and approval state. Log decisions for audits, not PII.
- Integrate: Wire up Declared Age Range (iOS) and Play Age Signals (Android), plus server checks. Add error‑handling for UNKNOWN status.
- Launch: Stage rollout, sandbox test parental flows, run UX copy tests, and train support.
Implementation patterns that work
1) First‑run age handshake
On first launch, call the age APIs. If the platform can’t return a signal (for example, unsupported region), fall back to your existing age gate. For minors, show a thin experience until parental approval is confirmed. This avoids bait‑and‑switch: you never unlock features you’ll have to revoke minutes later.
2) Entitlement guards at the edge
Represent age and consent as claims in your auth token (for example, age_band=16_17, consent=parental_approved). When tokens refresh, re‑evaluate and adjust entitlements. That way, revocations propagate quickly without real‑time fanout.
3) Significant change workflow
On Android, publish significant changes with an effective date in Play Console, then check the mostRecentApprovalDate and approval statuses in your app to determine access. On iOS, use app messaging to re‑disclose and restrict features until you re‑establish consent as required. (developer.android.com)
People also ask: FAQs we’re hearing from teams
Do we need separate builds for Texas, Utah, and Louisiana?
No. Build a single code path that detects the platform signal and regional applicability. Toggle disclosures and gating based on the signal and your server‑side policy. Avoid forked builds that become unmaintainable.
What counts as a “significant change”?
Patterns we’re treating as significant: switching to a subscription, enabling DMs or user‑to‑user interactions, broadening data collection, or changing the app’s age rating. If you’d consider a big banner in release notes, treat it as significant and be ready to re‑permission supervised users.
Will these laws force us to verify every adult with a government ID?
Platform‑level signals are designed to keep you out of the ID collection business. Apple provides age bands only; Google Play provides verified/supervised status and age bands in applicable regions. You shouldn’t be storing IDs yourself unless your specific business model requires it for other reasons. (developer.apple.com)
How do we avoid breaking conversion?
Don’t block the entire app while waiting for signals. Load core content, then progressively unlock paid or social features as entitlements verify. Keep purchase CTAs visible, and explain clearly if parental approval is pending—use time estimates in copy to reduce churn.
Data we know today (and how to use it)
- Texas SB 2420 is enjoined as of December 23, 2025; Apple paused Texas enforcement on December 24 while leaving dev tooling available for testing. Design your flows as if enforcement could resume with short notice. (macrumors.com)
- Apple’s Declared Age Range is shipping and documented. You’ll receive a coarse‑grained band—treat it as authoritative for UX and entitlements. (developer.apple.com)
- Google Play Age Signals (beta) returns verification/supervision status, age bands, and parent approval signals; you can declare significant changes with effective dates in Play Console. (developer.android.com)
- Utah and Louisiana are scheduled for mid‑2026 activation, so the multi‑state reality is coming even if Texas remains paused. Build once. (arstechnica.com)
Compliance UX: copy that reduces drop‑off
Short, plain language wins. For supervised teens, say: “Your parent needs to approve this change before you can use [feature]. We’ve sent them a request.” For adults in affected regions, say: “We’ll check your account age with Apple/Google. We never see your ID.” Put this messaging on the exact screen where friction happens—don’t hide it in a modal three taps later.
Testing: don’t wing it in production
Run sandbox accounts for both platforms. On Android, test SUPERVISED_APPROVAL_PENDING and SUPERVISED_APPROVAL_DENIED paths and ensure your server revokes entitlements immediately on denial. On iOS, script age‑band transitions and verify your feature flags adapt without requiring a fresh install.
Security and privacy trade‑offs
Two failure modes recur. One: apps over‑collect personal data “just in case,” which creates breach risk. Two: apps rely solely on client‑side checks, which bad actors bypass. Keep the band and approval state in read‑only claims signed by your auth server; the server is the enforcement point. Rotate keys, log policy decisions, and delete transient data you don’t need.
Organizational checklist: who does what
- Product: Define age‑band experiences and significant change policy. Own the copy.
- Engineering: Integrate signals, write entitlement guards, and build fallback paths.
- Legal/Privacy: Approve disclosures, ensure your privacy policy reflects age‑based processing, and map to COPPA/state privacy laws.
- Support: Prep saved replies for “pending approval,” “denied,” and “revoked” scenarios.
- Growth: Monitor conversion by age band and region; adjust gated upsells.
What to do next
- Map your app to age bands this week—content, social, and payments.
- Implement Apple Declared Age Range and Google Play Age Signals behind a server‑controlled flag.
- Design your “significant change” system for Android and a re‑consent plan for iOS.
- Run a sandbox week with supervised and adult flows; track friction.
- Update your disclosures and push a staged release.
Need a hand shipping this?
If you’d like an expert partner to blueprint and implement your age‑aware flows, our team can help. We’ve shipped privacy‑preserving monetization and consent systems for consumer apps at scale. Read our related playbooks—App Store Age Rating 2026, Play Age Signals: Ship Now and App Store Age Ratings 2026: Ship Without Blockers—and see how we execute on real deadlines. Then check our mobile compliance engineering services and get in touch.
Appendix: a minimal tech design you can copy
Here’s a concise blueprint we’ve used with clients:
Client:
- On app start, call platform age API; pass result to your server with device/platform attestations (App Attest / DeviceCheck on iOS, Play Integrity on Android).
- Render features based on claims from the server; never trust client‑side flags for paid features or social posting.
- For Android supervised users, poll Age Signals after you submit a significant change; if pending or denied, keep features locked and explain the next step.
Server:
- Issue short‑lived tokens with age_band and consent claims; store only the band and last approval timestamp per install or account.
- On purchase or gated action, re‑check the platform signal (or enforce freshness SLA on the claim).
- Expose an internal audit endpoint that dumps the decision chain for a given user action (no PII).
This design keeps you nimble as laws iterate and avoids painting yourself into a compliance corner.
The bottom line: treat age verification as an entitlement system, not a one‑off modal. Ship it once, keep it privacy‑first, and you’ll be ready for the next state that flips the switch.





Comments
Be the first to comment.