Third-Party Cookies in Chrome: What to Ship in 2026
Let’s cut through the noise: third-party cookies in Chrome aren’t going away this year. Google formally shifted strategy in July 2024, and UK regulators released their Privacy Sandbox commitments in October 2025. As of January 22, 2026, your roadmap should assume cookies remain available in Chrome—while Safari and many Firefox configurations still block them. That mix is the real constraint teams have to design for.
The 2026 reality check: what changed—and what didn’t
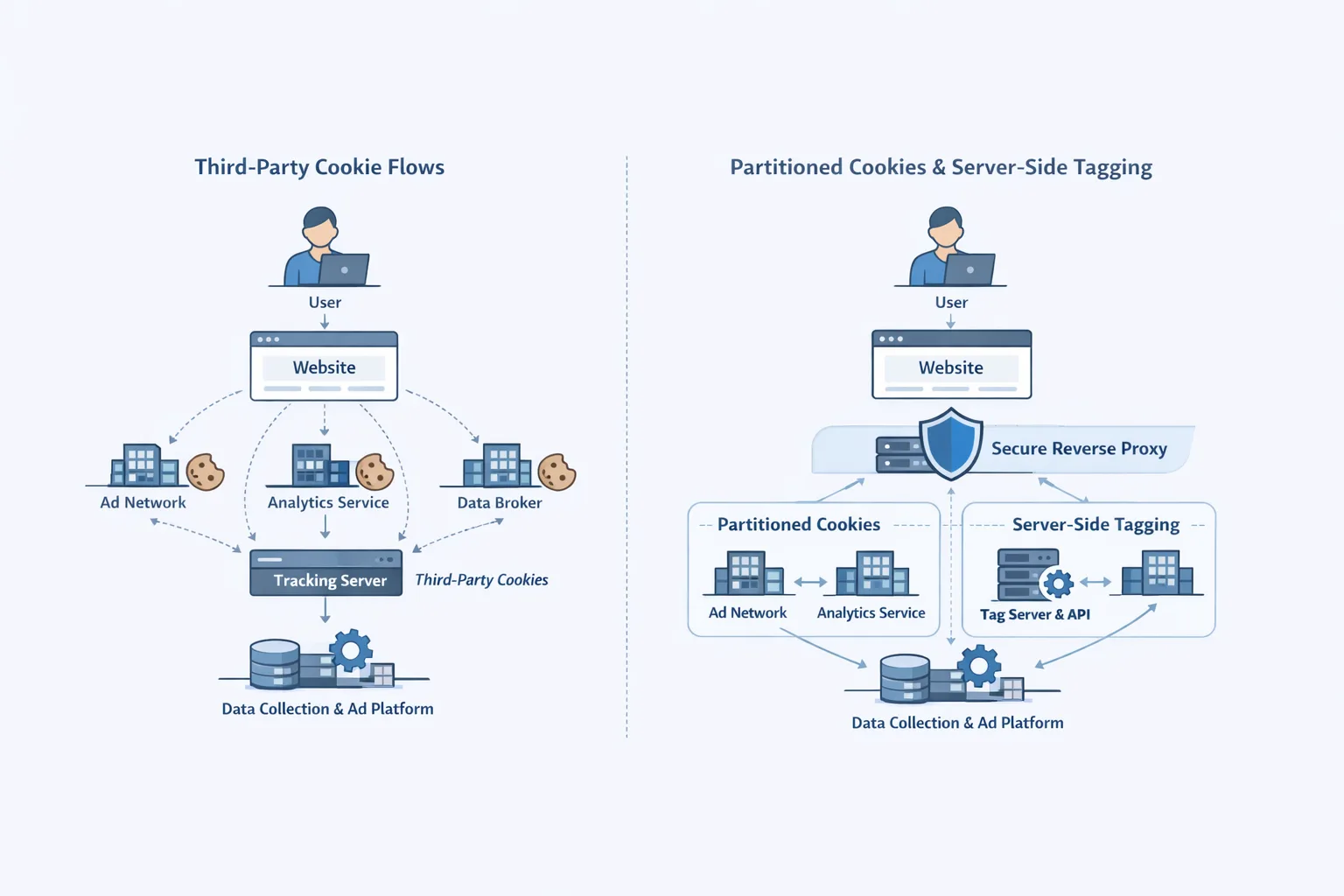
Here’s the thing: Google didn’t abandon privacy work; it abandoned the forced deprecation timeline. The Privacy Sandbox APIs (Topics, Protected Audience, Attribution Reporting, Shared Storage) are still in Chrome. FedCM is maturing for sign‑in flows. CHIPS (partitioned cookies) is shipping. But the binary on/off switch for third‑party cookies in Chrome is gone.
What didn’t change? Safari continues to block third‑party cookies by default and has long shipped Private Click Measurement (PCM) for aggregated attribution. Firefox users frequently run with enhanced tracking protections; experimental privacy‑preserving attribution didn’t go broad. The result is a mixed environment: Chrome allows third‑party cookies (with user choice and enterprise policies), while non‑Chromium traffic forces privacy‑first architecture.
If you lead growth or engineering, treat Chrome’s reversal as time you can reinvest—not a hall pass to keep 2018‑era tagging. The durable path blends first‑party data, server‑side endpoints, consent signals, and privacy‑preserving measurement where supported.
What this means for measurement and identity
Measurement: In Chromium browsers, the Attribution Reporting API offers click/view measurement without user‑level identifiers. It’s not a drop‑in replacement for last‑click cookies, but it’s good enough for incrementality tests, network comparisons, and directional return on ad spend when instrumented correctly. On Safari, PCM provides a parallel, privacy‑preserving route; design your event model so conversions can be reported to both stacks. On Firefox, assume less cross‑site signal and lean harder on modeled outcomes and first‑party analytics.
Identity and sign‑in: Federated Credential Management (FedCM) continues to advance. If you rely on Google Identity Services (One Tap/Auto sign‑in), plan and test FedCM so your SSO keeps working as browsers tighten cross‑site access. Don’t wait for a forced deadline to discover iframe, CSP, or prompt‑rate edge cases.
Embedded experiences: For third‑party widgets (chat, payments, media) that legitimately need state across embeddings, CHIPS enables partitioned cookies keyed to the top‑level site. It’s a safer option than generic third‑party cookies and avoids breaking legitimate cross‑site embeds when other browsers clamp down.
Primary question: Are third‑party cookies in Chrome really staying?
Yes—in Chrome. That’s the operative phrase. Expect more user controls and enterprise policies, but not a mandatory kill switch. Plan your stack to benefit from Chrome’s flexibility while remaining functional—legally and technically—on Safari and Firefox where third‑party cookies remain off by default.
A practical framework to ship now
Use this three‑bucket plan to avoid analysis paralysis in Q1/Q2:
1) Keep (but lock it down)
Keep third‑party cookies where they measurably add value on Chromium traffic, but harden them. Set SameSite=None; Secure and correct Domain/Path. Monitor lifetime and scope; right‑size TTLs. For embedded components, adopt Partitioned cookies via CHIPS to reduce cross‑site leakage. Enforce CSP and Permissions Policy to cap what third‑party iframes can do.
2) Modernize (make first‑party your default)
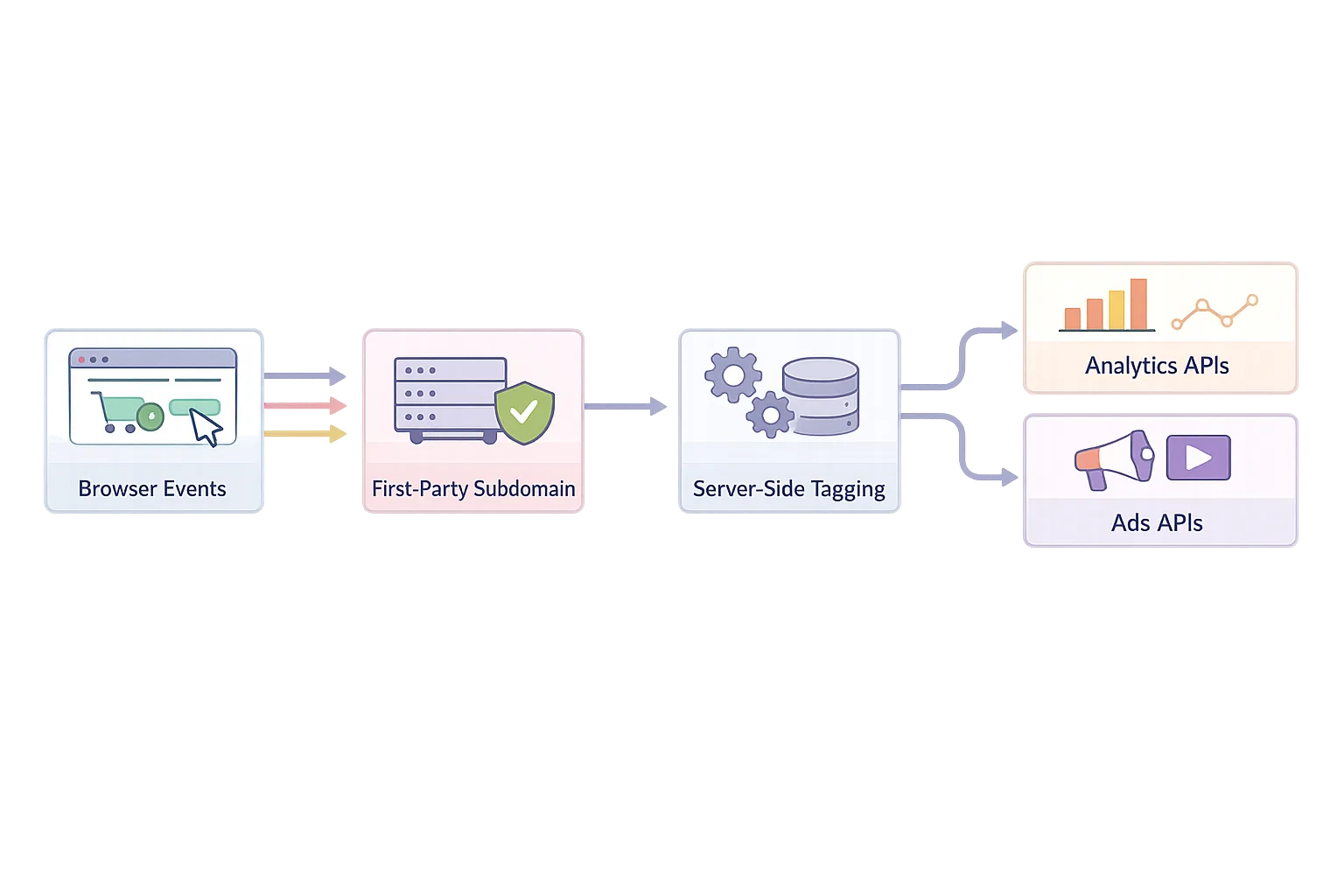
Shift tagging and state to first‑party subdomains you control (e.g., tags.yourbrand.com) and deploy server‑side tagging. This helps with ad blockers, improves latency, reduces PII spill risk, and sets you up for consent‑aware data flows. Align with a first‑party identity backbone: stable user IDs tied to accounts, hashed emails where permitted, and clear consent gating in your CDP/CRM syncs.
3) Replace (privacy‑preserving measurement)
Where cross‑site cookies are off, replace them with APIs built for privacy: Attribution Reporting on Chromium, PCM on Safari, and clean server‑side event streams to your analytics warehouse. Your objective isn’t pixel parity; it’s dependable directional measurement plus experimentation frameworks (geo‑split, holdouts, MTA/MMM blends) that stand up in audits.
Eight steps to productionize your 2026 plan
Step 1: Inventory every cookie and tag
List all cookies set by your site and third parties. Flag any with missing SameSite, unbounded TTLs, or unclear owners. Map cookies to use cases (auth, session, personalization, ads, analytics). Kill anything orphaned. Document data flows and recipients—your legal team will thank you when state privacy signals expand again.
Step 2: Partition where you embed
If you ship embedded widgets, opt those cookies into CHIPS with Partitioned plus __Host- prefix, Secure, and SameSite=None. Test across Chrome, Edge, and blocking extensions. Validate partitions in DevTools (Application → Cookies) and confirm fallbacks in Safari/Firefox where partitioning semantics differ.
Step 3: Move collection endpoints first‑party
Stand up server‑side tagging on a subdomain you own. Proxy critical pixels (ads, analytics) through that endpoint to reduce breakage and shield user identifiers. Set strict inbound validation and drop anything that looks like PII. This is where many teams pick up 3–7% event reliability on Safari traffic and improve TTFB by shedding heavyweight client code.
Step 4: Wire consent everywhere it matters
If you touch the EEA or UK, keep Consent Mode v2 live and accurate—this remains table stakes for advanced ads features, modeling, and remarketing. In the U.S., emit IAB GPP strings for applicable states and honor opt‑out/limit‑use flags consistently across web and mobile. Build your consent state into your data layer so downstream systems never have to guess.
Step 5: Instrument privacy‑preserving attribution
On Chromium, implement event plumbing for the Attribution Reporting API and validate end‑to‑end reports against your server‑side truth set. On Safari, enable PCM reporting endpoints. Expect fewer dimensions than cookie‑based reporting; plan to reconcile with lift tests and MMM rather than brute‑forcing user‑level joins.
Step 6: Prep SSO for FedCM
If your sign‑in relies on cross‑site iframes or One Tap, test FedCM now. Check your iframe allow and Permissions Policy headers, Content Security Policy, and prompt cadence. Expect a small UX change: some flows require lightweight user confirmation. Teams that test early avoid sudden conversion dips when browser UX adjusts.
Step 7: Cut dependency on opaque remarketing
Remarketing that only works with third‑party cookies is a liability. Rebase audiences on first‑party signals: product intent, lifecycle stage, and triggered events. Where ads platforms support it, send server‑side conversions with consent, hashed identifiers, and clear LDU (limited data use) flags for restricted regions.
Step 8: Prove it works—continuously
Set a quarterly testing cadence. Track event delivery rates by browser, consent availability, and attribution coverage. Trigger controlled geo or time‑based holdouts to validate causal impact. Publish a one‑pager internally after each round: what broke, what improved, what you’re deprecating next.
People also ask
Do I still need Privacy Sandbox if Chrome kept cookies?
Yes—because Sandbox features solve problems that regulators and non‑Chromium browsers won’t let you solve with third‑party cookies. Attribution Reporting, Protected Audience for on‑device interest groups, and CHIPS give you durable tools that degrade gracefully when third‑party cookies aren’t available. They’re additive, not merely replacements.
Will an enterprise policy or extension kill my cookies anyway?
Possibly. Many enterprises enforce stricter defaults or deploy extensions that block cross‑site tracking. That’s another reason to move collection first‑party, partition embeds, and maintain non‑cookie attribution. Treat Chrome as friendly but not guaranteed.
What about IP‑based tracking and browser fingerprinting?
Don’t. It’s brittle, increasingly mitigated by browser features (including Chrome experiments that reduce IP‑based tracking in private modes), and risky from a compliance perspective. Invest in consented first‑party data and modeled measurement instead.
Is server‑side tagging a silver bullet?
No. It improves reliability and control, but you still have to honor consent, avoid transmitting PII, and keep vendor contracts/data processors tidy. It’s architecture, not amnesty.
Risks, trade‑offs, and edge cases
Models will disagree. Attribution APIs, PCM, and MMM won’t produce identical answers; your job is to choose the signal that aligns with strategy and auditability. Consent drift happens—one stale CMP configuration can silently cut off remarketing or measurement in key regions. FedCM migrations break when an iframe policy or CSP blocks the prompt. And if you embed third‑party tools, a missing Partitioned attribute can bleed state across customers’ sites, creating data protection headaches.
There’s also the temptation to pause everything “until the dust settles.” That’s how stacks calcify. The teams that win treat 2026 as the year they reduce third‑party cookie dependence while still monetizing Chromium traffic responsibly.
What to do next
- Book a two‑hour cross‑functional review—growth, dev, data, legal—to approve the eight‑step plan and owners.
- Stand up a first‑party tag endpoint and ship your first server‑side conversion within 30 days.
- Enable Privacy Sandbox attribution on a single paid channel; run a four‑week shadow test against cookie‑based numbers.
- Audit consent: EEA/UK (Consent Mode v2), and U.S. state GPP signals. Fix gaps.
- Kick off FedCM testing for your SSO and embedded sign‑in flows.
If you want help pressure‑testing your plan, our team runs hands‑on privacy‑first analytics and growth engineering sprints. See what we do in delivery, browse a sampling of past work in our portfolio, or reach out via our contacts page. For ongoing tactics and release‑driven playbooks, keep an eye on the ByBowu blog.
SEO angle: capture intent the right way
Searchers right now ask two things: “Are cookies dead?” and “What should I implement instead?” This piece answers both and gives a path you can execute in the next sprint. Use the primary query—third‑party cookies in Chrome—to anchor your internal documentation and redirect old “cookie deprecation” runbooks to this 2026 plan. Your growth depends less on the existence of cookies and more on whether your stack can thrive when they’re present on one browser and constrained on the others.



Comments
Be the first to comment.